This Week in Enterprise Tech 571, Transcript
Please be advised this transcript is AI-generated and may not be word for word. Time codes refer to the approximate times in the ad-supported version of the show.
00:00 - Curt Franklin (Host)
This weekend enterprise tech, where we talk about getting more than you should out of generative AI, why we have PLC still getting us in trouble years after Stuxnet made the scene, and a deep, deep dive into DNS Quiet on the set.
00:27 -
Podcasts you love from people you trust. This is TWiT.
00:41 - Curt Franklin (Host)
This is Tweet this weekend, enterprise tech episode 571, recorded December 1st 2023. Dns deep dive part one Demystify DNS.
00:56 - Lou Maresca (Announcement)
This episode of this weekend enterprise tech is brought to you by Collide. Collide is a device trust solution for companies with Okta, and they ensure that if the device isn't trusted and secure, they can't log into your cloud apps. Visit collidecom. Slash twyatt to book an on-demand demo today. And by Bitworn, the open source password manager, to help you stay safe online. Get started with a free teams or enterprise plan trial, or get started for free across all devices as an individual user at bitworncom. Slash twit and by our friends at ITProTV. Now. Aci Learning ACI's new solution insights assists in identifying and fixing skill gaps in your IT teams. Visit goaceilearningcom. Slash twit. Tweet listeners can receive up to 65% off an ITPro Enterprise solution plan after completing their form. Based on your team's size, you'll receive a properly quoted discount tailored to your needs.
01:58 - Curt Franklin (Host)
Welcome to Twiyat, your weekly guide to everything that's worth knowing in the world of enterprise technology. I'm Curt Franklin, your host for this episode. You'll notice that we don't have Mr Lou Moriska here, not because he's on assignment, but because we have a special edition of this week in Enterprise Tech coming up this week. Tell you a little bit more about it later, but let's just say you're going to get the advantage of us sinking our teeth deeply into a very, very juicy Enterprise Tech topic. But before we do that, I've got to welcome my co-host, mr Brian Cheeb. Brian, so have you managed to recover from Orlando Maker Faire yet?
02:55 - Brian Chee (Host)
My knee is still a little swollen and so forth, but other than that I'm pretty good. I was actually able to go right around the fairgrounds in a snorkel lift adding more fiber optics and trying to expand the network All kinds of fun and games. And I think it's okay to say that Lou had a day job function that he could not get out of. So it made scheduling easier because Ross and Josh co-authored a book together on DNS and security aspects, so we thought it'd be a lot of fun to have both of them on and go to two hosts.
03:40
So we're going to be playing a host shuffle the next three weeks because this is a three-part series where we're going to dig very deep into DNS, which I will say is one of the least understood technologies but most used. Everybody uses DNS. Nobody likes typing in IP numbers, especially long IPv6 numbers. So DNS is a very, very important technology and most people just use it. They don't understand it. So Ross and Josh are going to go on a deep dive and in order to do that, we're dropping out a few of our normal pieces, we're dropping out the bytes, so we have more time because there's a lot of ground to cover and I'm really looking forward to it.
04:31 - Curt Franklin (Host)
I think this one is going to be a lot of fun. And, as you say, DNS is one of those technologies on the internet that literally everyone who uses the modern internet has taken advantage of. But most people, even if they're aware that DNS exists, they don't know what it does and how it does it. By the time we get through with this series of episodes, that won't be the case anymore. But before we can dive into DNS, we do want to bring you the blips.
05:11
Researchers have found that a simple hacking technique can get chat GPT to cough up training data. A news article on dark reading has news of a report published this week in which researchers described how they got chat GPT to spew out memorized portion of its training data merely by prompting it to repeat words like poem, company, send, make and part or ever. Now here's how it worked. When the researchers prompted chat GPT to repeat the word poem forever, the chatbot initially responded by repeating the word, just as it had been asked to do. But after a few hundred times, well, it got bored and chat GPT started generating nonsense output, and in that nonsense output there was a little bit that included memorized training data like personally identifiable information and personal contact information. Now it will not surprise you to hear that not all one word repeats have the same results. For instance, prompting the chatbot to repeat the word company caused it to emit training data 164 times more often than if you ask it to repeat words like no, that's K and O? W, not N? O.
06:41
Data that the researchers were able to extract from chat GPT in this manner included personally identifiable information on dozens of individuals, as well as explicit content when the researchers use one of the seven words you can't say for television as a prompt, verbatim paragraphs and books and poems when the prompts contain the word book or poem and URLs, unique user identifiers, Bitcoin addresses and programming code. Now, journalists at dark reading weren't able to duplicate these results, but again, this isn't going to surprise people who know generative AI. What they don't know is whether the difference was the result of a patch to the engine or just a difference in how it responds to different prompts. We do know that a lot of researchers are trying to find examples of this threat that's called a divergence attack. As long as AI engines are capable of memorizing verbatim input information, threat actors are going to be looking for ways to get it back out. This is not going to go away anytime soon. Stay tuned to see which side is on top in this particular long running contest.
08:07 - Brian Chee (Host)
Well, if you've been watching Twilight for any amount of time, you know I am very, very high on the concept of virtual desktop infrastructure, or VDI, and I've included VDI taking over the world in quite a few different episodes and I've gone on all kinds of rants. Well, I get validated. So, considering Microsoft's been quietly pushing the VDI concept ever since server 2012 release two, it comes not as any surprise that this new product has finally arrived into Office 365 family. What I predicted is VDI will appear as a desktop as a service offering in the form that utilizes HTML5, so they can be implemented on just about any modern platform. What I'm expecting is announcement from big ISPs like Spectrum and AT&T as a bundled offering. So here's my prediction for the new year.
09:14
I'm suspecting, sometime in 2024, that a DOCSIS based HTML5 desktop of us as a service offering will appear as a way to lock customers into a higher end broadband system. I should add that this initial offering is a virtual app, not a full desktop. Yet at the moment, desktop as a service is most likely around the corner, as the bean counters decide if they can make money with full virtual desktops. So, just as a reminder, this desktop as a service will eventually also become a gamer's platform due to Microsoft's ability to leverage maximum use out of shared GPUs. I compare it's operation like a game of Tetris to share GPU portions in Hyper-V servers. I hope this was going to happen. I've been praying, it happened and now I'm getting vindicated. So I was really hoping to be able to play with this, but when I tried to sign up for the service, I got a message the beta is full. When I tried to sign up kind of a bummer. Now I need to also add a tag to this.
10:38
Virtual apps with shared GPUs is not primarily Microsoft. Citrix, vmware has it and so does quite a few other virtual virtualizing systems. It's all in type one hypervisors where you install and bear metal. However, when you have a marketing engine that is Microsoft, get behind the technology. Now, all of a sudden, we've got enough oomph behind it that we might finally see it. And now that I'm long removed from my non-disclosure, I had a project with the folks at CenturyLink. I was actually working quite a while ago almost a decade now on implementing this exact thing through using desktop boxes for CenturyLink customers. The idea was to go and sell a premium service so you can run all kinds of things. I have done lots of stuff with VDI and one of the biggest projects was with the University of Hawaii School of Architecture and we got a server running Revit, so 3D modeling of buildings at the University of Hawaii, and the students were able to do as-built drawings of the University of Hawaii buildings from iPads with a Wi-Fi connection. So it's got a lot of promise and I'm crossing my fingers.
12:17 - Curt Franklin (Host)
Hey, remember that whole global pandemic thing? Remember the hundreds of thousands of people who lost their jobs when business around the world crater? Well, at that time, most of the tech industry seemed immune to the layoffs, as the IT universe staffed up to deal with all the companies moving work online when folks decided not to leave their houses and do everything on the web. By the second half of 2022, though, tech companies started to initiate significant layoffs. This was especially shocking following an extended period of what amounted to frenzied tech hiring and attention to the employee experience.
13:04
Now, standard explanations for the tuts were that companies hired too many during the pandemic and that they were looking at the specter of a recession in the months ahead. The recession still hasn't happened, but layoffs continue through this month, as companies like Broadcom, unity, dataminer and VMware, among others, have cut hundreds to thousands of employees each. While some of the layoffs come in response to mergers or acquisitions and others are the result of significant revenue drops or business declines, many seem like preemptive layoffs in anticipation of the same recession that they were predicting last year and that some business leaders still see as all but inevitable. Now, while the economy as a whole continues to chug along, these ongoing layoffs are really all the proof we need that the IT world is not immune to the sort of business slowdown and response that can hit any industry. So be gentle with your high tech colleagues. They're not nearly as secure as they felt just a couple of years ago.
14:31 - Brian Chee (Host)
A big thank you to the folks at Dark Reading for this article. This is something I've been following for decades, ever since we first started hearing about Stuxnet. The headline's interesting. This is the first time I've seen a headline where they've actually named the name of the PLCs that are so vulnerable. It's our friends at Siemens, so the article is Siemens PLCs still vulnerable to Stuxnet-like cyber attacks.
15:02
So programmable logic controllers, plcs that were vulnerable to the Stuxnet attack are still in use globally and rarely have security controls deployed, meaning they're still at risk More than 10 years after Stuxnet. New research shows users rarely switch on security controls, such as using passwords, and feel updates are too cumbersome to be applied. Colin Fink, tech lead of reverse engineering and connectivity at Enlize, says the Siemens proprietary protocol, which is used to read and write data as well as to program the series 7 PLC, has the problem. However, this is only protected by obscuffation, while the researchers were able to bypass it all. All right, warning rant along. Plc program is confusing, convoluted and, in general way, harder than it needs to be in this day and age. They served a need for replacing really complex clockwork gear assemblies to control things like throttles, rudders, valves and many of the components of modern industrialization. However, when PLCs first started appearing as a substitute, computing resources were very scarce and PLCs allowed designers to trigger motions or actions by sending very small pieces of data to control what happens. The pain point in these PLCs were that they were designed in a much simpler and kinder world and a large number were controlled with much slower serial connections, like RS-45 ModBust, measured in, at best, kilobits per second, whereas networks are measured in megabytes per second.
16:57
It's said that you could crash some PLCs simply by sending a half dozen pings in a row against that target. Ouch Well, the big problem in my mind and my opinion is friction from regulators. For instance, it took nearly five years to get permission from the American Bureau of Shipping to change out ancient thick ethernet that's super vulnerable to noise created by running them next to high voltage power lines typical of diesel electric ships. I just wanted to change the PLC connection from thick ethernet to RF immune fiber optics so that we could avoid the vulnerability of noise induced by the power lines that are run parallel with the thick ethernet, especially as it goes through waterproof bulkhead blocks. Industry name for those are rocks blocks.
17:59
Anyway, to respond to the article statement about it taking too long to change our ancient PLCs out. I answer that it's friction from regulators, costs of lots of PLCs doing tiny actions and too many educational institutions that don't teach any of this anymore. I mean, what's the last time a computer science student has ever even heard the word PLC? Josh, I'm going to bug you about that, because I was one of your instructors and I don't think anyone mentioned that except for me. Yeah, josh is shaking his head, so I think I was the only instructor at the University of Hawaii that even mentioned PLCs. Anyway, end rant. Thanks a lot.
18:46 - Curt Franklin (Host)
Well, that's the end of the rant and the end of the blips. We've got a lot more quiet to go, but before we can go to the next segment, we need to hear about an advertiser, and there's nobody better to do that than Lumoresco.
19:03 - Lou Maresca (Announcement)
Well, thank you guys. I'll get you back to Enterprise and IT News in just one moment, but before we do, we do have to thank a really great sponsor of this week at Enterprise Tech, and that's Collide. Collide is a device trust solution for companies with Okta, and they ensure that if a device isn't trusted and secure, it can't log into your cloud apps. If you work into security or IT and your company has Okta, I guarantee this message for you.
19:26
Have you noticed in the past few years, the majority of data breaches and hacks you read about have something in common. That's right. It's employees. Sometimes an employee's device gets hacked because of an un-patched software. Sometimes an employee leaves sensitive data in an unsecured place, and it seems like every day a hacker breaks into using credentials they've phished from an employee.
19:48
The problem here isn't your end users. It's the solutions that are supposed to prevent these breaches. It doesn't have to be that way. That's right. Imagine a world where only secure devices can access your cloud apps. In this world, phished credentials are useless to hackers and you can manage every OS, including Linux, all from a single dashboard. But, best of all, you can get employees to fix their own device security issues without creating more work for your IT team. The good news is, you don't have to imagine this world. You can just start using Collide. Visit collidecom slash twyatt to book an on-demand demo today and see how it works for yourself. That's K-O-L-I-D-E dot com slash twyatt and we thank Collide for their support of this week in Enterprise Tech. Back to you guys.
20:40 - Curt Franklin (Host)
We look forward to hearing more from you later on. Well, normally, as Brian said earlier, we'd be heading to the bytes now, but instead we're going straight into our intensive episode, first of three, on DNS. And to walk us into that topic, I'm going to turn it over to my co-host, brian Chee. Brian, take it away.
21:09 - Brian Chee (Host)
Well, we've had lots of people on. One of the fellow workers at Infoblox, mr Cricket Liu, has been on the show and he talked a little bit about the origins of DNS. He was actually a digital equipment corp and got thrown in the deep end, shall we say. Domain name service is probably one of those services that well, everybody uses it because you don't like typing in numbers. I wasn't too bad at typing in 128, 171, 104.10 if I wanted to go and log into one of my old lab servers, but it's a lot easier to type in, say, wauzaanclhawaiiedg, because it's a human interface. So everybody uses DNS. However, there's a lot of things happening under the hood. So, in response to viewer requests and I'm going to use the word request lightly, because some of them were downright demands we wanted to do a deep dive, and a deep dive's goal is to try and look under the hood, try and talk about the ramifications for enterprise users and, especially in this day and age, talk a lot about the security issues, because DNS was invented and came to popularity in a kinder, gentler world and, unfortunately, with cyber attacks and all kinds of other nasty things happening on the internet, dns needs to catch up and we're definitely going to talk about. So episode one is called demystifying DNS basics and recursive DNS. So we're going to talk about the fundamentals of the DNS technologies, look at the design considerations for reliable client name resolution and what is protective DNS and how does it apply to DNS lookups.
23:14
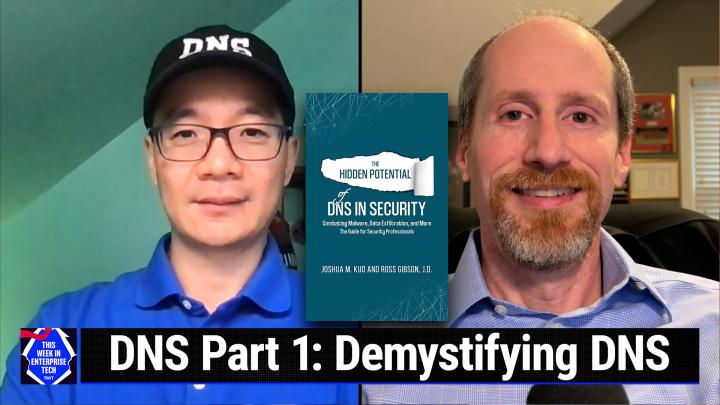
So to do that, we have our two friends. We have Ross Gibson, principal Solutions Architect at Infoblox, and Mr Josh Kuhl, who calls himself a DNS expert. He was one of my ex-students at the University of Hawaii and together they wrote a book. In fact I see it on both of their bookshelves over their shoulders. So, mr Ant, if we could go and bring up the title, we have an Amazon link if our viewers want to look at it. But we're going to start off with what is your origin story? What did you do? How did you get to where you are now? So let's start off with Ross and then we'll sort it over to Josh Ross. What's your origin story.
24:08 - Ross Gibson (Guest)
Well, thanks, Brian. My story starts back in the late 90s when I started out actually in network management systems. Then I moved into more traditional networking route switch. Then I took a little diversion into law and actually practiced law for a little bit before coming back in IT and by mistake ended up falling into DNS, which is what I've been doing for the past almost 15 years now.
24:34 - Brian Chee (Host)
Awesome, Josh, other than being one of my ex-students. What else happened? How did you get to where you are after you left the University of Hawaii? What was the path to get to Infoblox?
24:49 - Josh Kuo (Guest)
Okay, yep. So after spending quality time with Brian at the networking labs in Hawaii, I hopped through a series of different jobs covering software programming, security consulting, systems administration, network automation, design and, similar to Ross. After a series of jobs, I ended up on DNS, because DNS, as we will see, is sort of a where all these fields come and meet. You'd need to know some networking, some systems, some security to really be an effective DNS architect.
25:32 - Brian Chee (Host)
Very cool, josh, thank you very much, and thank you for being both of you, for being guinea pigs. We've been wanting to do a deep dive on technologies like DNS, and thank you so much for playing our game. So here's some things. Why DNS? Is there enough neat to talk about this for three episodes? Let's see. Ross, you want to kick this off, or is that a Josh question?
26:03 - Ross Gibson (Guest)
Sure, I can start off with that. What I would say about it is DNS is one of those technologies where people have a surface-level view of it. As you said, everybody uses it and they know it translates names and IP addresses, but when you get into actually implementing, that's where the detail lies. It can be very simple in theory, but in actual application it can become incredibly complex and, as you mentioned, it's kind of a three-part series and there are three main categories of DNS that you find in the enterprise world. You've got your external authoritative DNS, which is what's facing the internet, so that's where your website, your dub-dub-dub entry, would be, so that's the world coming towards you. And then you've got the two internal pieces, one being authoritative data inside, which we'll talk about on the third episode. And then we have today's subject, which is recursive DNS, which is your internal clients going out and resolving namespace outside of your organization.
27:08 - Brian Chee (Host)
Well, let's go and elaborate just a little bit. A lot of viewers are running either by choice or by inheritance technology called Active Directory. One of the major pieces is domain name services for internal use. So I guess the question is what really is DNS for the enterprise? How is it different from, say, dns for a mom-and-pop shop or an internet service provider? So let's kind of slice and dice DNS a little bit and start talking about the different types and what's going on. So let's toss this one to Josh Josh.
27:54 - Josh Kuo (Guest)
Okay, sure. So Ross already sort of quickly broke down the three major components. So today we're going to try to focus in more on how do I look up a name when you know, for most users, home or enterprise? You fire up your device, whatever it is Maybe it's an app on your phone or it's a web browser on your computer type in something either a URL or whatever name, and, bam, magic happens. Packets flying around and then you get something that shows up on your screen. Well, dns is in there somewhere. So that's the part we want to focus a little bit more on today is how does that transpire? And then in the next two episodes we'll dig deeper into some of the other components. So sorry, I didn't prepare a lot of diagrams, but I'm going to just say in your head imagine two sides of the world.
28:58
You have DNS servers. A lot of times we just call it DNS, dns, like it's one big thing, but it's had. It has at least two separate functions. One is looking up what I call answer seekers. It's out there looking for answers, and then you have the answer keepers, the servers that have the answers. So they're both DNS servers, but they do very different functions. So today we're focusing on seeking, and that's what we call recursive DNS. You ask the DNS server whatever question it is, it goes out, a lot of magic happens. It usually goes to root, to whatever, and follows through and find you the answers. So I think I'll pause there and throw it to Ross to see if he has anything he wants to add or get deeper to that on that.
29:49 - Ross Gibson (Guest)
I think I think you're right to point out kind of the two, the seekers versus the keepers. I like that use of terminology. I think it's actually a pretty app description of it. The thing about recursion is that, as you mentioned, it's seeking, it's somebody's asking a question and wants to know how to get to a site, to a server, whatever it may be, and that process it happens actually pretty quickly, but there's a lot going on in there.
30:18
As you mentioned, there's the root servers and then you've got the TLDs, which would be things like com and edu and org, and then you've got the second level, below that, which generally is an enterprise in a lot of cases, so that could be Google or Apple or whatever it may be. And then you've got dot com, which is your TLD, and the resolution actually works backwards from the way that we would normally read it in most languages, or at least in English. You would read it left to right, but the resolution actually works right to left. So you start at the root, which is actually implied at the end of every name. So there's actually a trailing dot after com and then an implied root and that ties to the root of the DNS that is used across the internet and then from there you move down to the com servers and then to Apple or Google, whatever it may be.
31:13 - Brian Chee (Host)
I think what we've probably ought to do next is let's define some of these terms that you use. Very few people actually understand where a top level domain comes from, who manages it, and if I'm, say, at a university and I'm trying to talk to something in the commercial world, what's the flow? How does my DNS look up? Actually work? Who wants to take that one?
31:43 - Ross Gibson (Guest)
Josh Kahn. I'll start out and Josh can fill in some more details if I miss anything. So, as I mentioned, the root servers which are operated by actually a host of different organizations across the world. There are 13 roots, and the reason that there are 13 roots is because that's how many could fit in the packet without having to switch to TCP originally, and that's why there are 13. And so your typical DNS server has a list of all the root servers and it will randomly pick one of those servers and it will reach out to it and say I need to go to com, and then that root server will return a referral to com, so it will give back an information on what the name server's names are, and it will also give what's called a glue record, which is the actual a record information with the IP address of that next level server.
32:39 - Brian Chee (Host)
Josh Kahn. All right, so who runs these top level domains and these servers? Josh Kahn.
32:47 - Ross Gibson (Guest)
So the ICANN runs the kind of management of the TLDS. As far as allocating them, josh Kahn, there were originally ones that were purpose built, like com for commercial, edu, for education or for non-governmental organizations, for example, and then a few years ago, icann actually ended up selling customized TLDS, so things likegoogle, for example, so people could go out and register for whatever custom TLD they wanted and if they were approved, they would be what's called a registry for that domain. They would own it and thus could then sell it. Now, most people don't typically work with the registries, so the interface for actually buying a domain, for example, would be what's called a registrar, things likegoDaddy, namecheap and the like, and that's where somebody would go and say I want to buy companycom and you would buy it from them for a year, two years, three years, whatever it may be, and then they connect to the registry and the registry will then put the DNS entries in there to connect between whatever their TLDS and your servers that you're specifying.
34:10 - Josh Kuo (Guest)
Josh Kahn and I'll tie this in to enterprise. Why does the enterprise? Why is this important, josh Kahn? So very often people especially I think, the audience of the show probably remember days when, predating DNS, that you just have the hosttxt file and some may still be using it. People may think well, I can memorize IP addresses really well. If DNS goes away, not a problem for me. That's no longer true and I would urge our live audience you can try this now. Look up your favorite website. You know you come in website the good Amazon or Facebook Now type that IP address into the web browser. It's not going to work.
34:58
The modern applications are no longer tied to IP addresses, they are tied to the names. The SSL or TLDS certificates are tied to names. Email, which has been with us since the very beginning, never had IP addresses in it. I don't care how good you are at memorizing IP addresses, you can't send emails without DNS and your enterprise will stop working if you can't have emails. So this is kind of tying to the whole. Why is DNS so important to the enterprise? If you're a home user, you can't receive email. Maybe that's not a huge issue, but if you can't get your purchase order sent out or receive invoices from your customers, then that's a big issue.
35:47 - Curt Franklin (Host)
Okay, well, we are barreling along learning about DNS and this is great stuff, but we're going to press pause for just a minute and go hear about another sponsor of this week at Enterprise Tech Lou over to you.
36:06 - Lou Maresca (Announcement)
Well, thank you guys. We'll get you back to your enterprise and IT news in just one moment, but before we do, we'll thank another great sponsor of this week at Enterprise Tech, and that's our friends at Bitwarden, the only open source cross platform password manager that you can trust. Security Now's Steve Gibson has even switched over. With Bitwarn, all of your data, all the data in your vault, is end to end encrypted, not just your passwords. Bitwarn protects you by creating unique usernames and adding strong, randomly generated passwords for each of your accounts. Using any of the six integrated email alias services, you can log in a Bitwarn to encrypt your entire vault using SSL on an registered, trusted device. No master password is even needed. On top of that, being public to the world, bitwarn has professionally third party audits performed yearly and published on their website. You can even view all of Bitwarn's code on GitHub.
37:01
Share private data securely with customizable, fully customizable plans for personal or business needs. Start with a personal plan, free forever, and get unlimited devices and limited passwords and password and past key management. Or you can enjoy premium features by upgrading to premium account for just less than a dollar a month. And for only $3.33 a month, their family plan will give you up to six accounts with premium features and unlimited sharing and collections. Their enterprise plan is just $6 per user per month and they now have a team starter plan which is a flat $20 per month for 10 users, which provides a great value for smaller teams with all the premium features. Or pay $4 a month per user with teams of 11 or more.
37:49
Join Bitwarn at the fourth annual open source security summit, where businesses, open source enthusiasts, developers and security thought leaders can come together to explore how open source software leads to stronger cyber security. Headliners this year include Brian Krebs from KrebsOnSecuritycom, white Hat Hacker and CEO, social Proof Security, rachel Tobak, and generative AI expert and advisor, zach Cass. Join the leaders in open source security and register now for the open source security summit on December 7th at opensourcesecuritysummitcom. At TWIT, where bands of password managers get started with Bitworn's free trial of a team's or enterprise plan, or get started for free across all devices as an individual user. At bitworncom slash TWIT. That's bitworncom slash TWIT, and we thank Bitworn for their support of this week in Enterprise Tech. Now back to you.
38:50 - Brian Chee (Host)
You know we're starting to touch on enterprise. But one of the big questions you know, especially when you're starting with small to medium sized businesses, why not just use Google 8888, you know 8.8.8.8.8. What are the advantages of running your own DNS? And one thing I'd like to toss in is an awful lot of people use these small routers and when they send out dynamic host configuration protocol, they almost always point back to themselves for DNS resolution. Are we looking at a world to hurt someday in the future? So why don't we tie those together? You know why not use Google for our DNS? And are we falling into a pit of despair by using really cheap routers for DNS?
39:53 - Ross Gibson (Guest)
So I, yeah, I love the question about why not 8888? Because, like you said, you know, particularly for those before they become a big enterprise, they'll tend to use a free service like that and at the end of the day, you get what you pay for right. Not that 8888 is not a great service, it absolutely is but if you don't pay for the service, you have no SLA right. So if they're down for an hour you have no recourse. You also have no control or visibility. You also are giving up your data, which who knows what they're doing with.
40:26
There's actually a small section in the book that talks about, kind of some of the differences in data policies that you come across with those and how that may differ.
40:37
As far as tying into your routers, I don't know that that's necessarily problematic, other than the fact that you don't know what it's using, because in most cases they are not doing the recursion on their own.
40:53
They're using something like 8888 or, let's say, cloudflare or Quad9, which, again, for a home user, perfectly useful, definitely worth doing, rather than trying to run your own DNS server. But from an enterprise perspective, it's really something that you either need to be contracting with a provider that's giving you protective DNS services, which I'll come back to in just a minute, or running your own recursive DNS servers. As far as protective DNS servers, what that is is taking a DNS server and integrating threat intelligence data into it to review those known malicious domains against the query that you have coming in and then implement policy. That policy could be returning a negative response, saying it doesn't exist, or it could be redirecting it to some other server that you have, or a proxy server or something like that, and the protective DNS service has really been a growing industry as a whole and it's really critical. Any enterprise should be implementing some measure of DNS security today that you can't afford not to.
42:09 - Brian Chee (Host)
Well, since we're diving into enterprise and protected DNS and so forth, I think, kurt, you've been talking to a lot of the folks in the C-suite and various other people that control budgets. What have you been hearing when you put your ear to the ground?
42:31 - Curt Franklin (Host)
Well, it's interesting because it seems like a lot of companies don't want to spend money they don't have to for running their own DNS server, so they love the idea of going to a service provider for secure DNS.
42:49
On the smaller side of the enterprise the mid-sized company and especially the small company they don't want to have to buy the expertise required to set these up, much less have the hardware and software available to take care of it.
43:09
But one of the things I hear from a lot of people, especially the executives you know, we all know just how much of a strain a good high level executive can put on the system is that when they're out in the world let's say they're at their local large coffee shop, large chain coffee shop, and they want to get work done Now at their enterprise they have hardwired in, they have defined the address for a DNS server. They get to coffee shop X and all of a sudden they can't get on the network. You know it just will, not they. They see the network there. They may even be able to make the layer one attachment, but they can't find the Internet. What's going on? Is there a consistent issue? Is there some technology that's at work there that's keeping them from successfully navigating the conversation that would get them on the web.
44:27 - Josh Kuo (Guest)
Okay, I'll start and I'll let Ross finish my train of thoughts. So some of that could fall into the realm of NAC, network access control, which really is not, you know, not separate from DNS and DSEP. Where this could you know? So now we're talking about there might be sanctioned, officially sanctioned DNS service providers and we're saying, if you're a year, we don't care what your position, your title is. If you move out of the company, you're not using the officially allowed DNS servers. We don't want you to look up any names. That can be achieved in several different ways. One of the most common ways is some kind of agent, some kind of software lives on your device that is redirecting your DNS lookups, black calling it or, you know, pointing somewhere. So when you look up a name, it just doesn't go anywhere. So it creates the feeling that you can't get on the network. You are connected but all your DNS lookups just go nowhere and return no answers. So that is. I'll hand over to Ross to finish, because he may have some more stuff to add on this topic.
45:47 - Ross Gibson (Guest)
So it does kind of feed off of the whole neck piece, particularly in the coffee shop scenario that you laid out.
45:55
Quite often you've got a captive portal and basically what the captive portal is doing is, in a lot of cases, basically just giving you some terms of service. Could be, if you're at another enterprise, somebody has to sponsor you, right? So somebody that's actually a user there might have to sponsor you, put you in as a guest and what happens is it will drop you into a VLAN that's not routable externally and until you go to that captive portal, which basically is usually a specialized DNS server that's going to send you. Just, no matter what you look up, it's going to send you to this one address and then when you go to that portal it will actually enter your MAC address in most cases into the DHCP server and then when you renew you get a different address on a routable network and then you actually can gain access to the internet from there. That's in most cases in a coffee shop or some other business. When you're joining a guest network, that's usually how the DNS plays into that security mechanism.
47:03 - Curt Franklin (Host)
Very good, and I think one of the questions when you're talking about this is whether that is the only way that is available to these coffee shops and others to make sure they get stuff out. I've heard rumors for a while of solutions that don't involve captive portals, because it seems like people like you and Josh really hate captive portals because it tends to mess up all kinds of good, solid DNS security. Is that the sort of thing that we're going to have to live with for the rest of well, our careers, or are there solutions out there that would give people the security without messing up the security of DNS?
47:57 - Ross Gibson (Guest)
It's one of those things where because a lot of cases they've got to put in, of course you would ask me this question, but it's the lawyers, right? They're the ones that say, hey, you've got to put up these terms of service so that people know that we're not giving them any expectation of privacy or whatever the terms may be. So DNS is just a really efficient way to do it, because it's generally the first thing that's being hit, which is the same reason that it's a great security tool, because as soon as you try to go anywhere, the first thing that your computer is going to do is a DNS query, and so I don't know that getting rid of captive portals is the answer. I would say I've seen more enterprises, particularly like in an actual enterprise space, using protective DNS on their guest networks as well as their enterprise network. So they're maybe a different policy, a less restricted policy, but they're still providing some measure of protection for their guest users as well.
49:05 - Josh Kuo (Guest)
And I'll elaborate more from that, because I do hear a lot of confusions. Dns has a lot of very confusing terminologies and we keep inventing more that we're just really not helping. So the idea of DNS being one of them was invented around 2020-ish, so the current definition for it is it mostly applies to recursive when we're looking up names. So, for example, if I typed in you know, steal my credit card number dot com, then if you have a protective DNS server, it would have some kind of intelligence to know well, that is not a safe place to go. So in order to protect you, Josh, I'm going to lie to you. Instead of resolving, you know, giving you the IP address of this domain name, it would tell me you know, whatever the policy says, usually an ex-domain, which means it doesn't exist.
50:02
Now, that's technically a lie. The domain does exist. It probably has an IP address in Russia, but the DNS server is protecting me. So it's protective DNS and that is one of the key, probably the newer features that we want your listeners and viewers to be aware of that if you have a DNS architecture designed maybe 10, 15 years ago that you've inherited, this technology was not around back then. This is and you should know about protective DNS and think about how you can add it to your recursive DNS architecture so that it's filtering out, not taking the enterprise users to malicious places.
50:52 - Ross Gibson (Guest)
And then the other thing I would add on top of that before the technology as you said, Josh existed to do this type of filtering, some enterprises would actually build false root servers internally, which basically prevented them from looking up anything outside. Personally, I think that's a very problematic way to do things, particularly today, with the expansion of cloud technologies. Right, People need to look up domain information outside of their enterprise in order to function on even what would be considered internal applications. So that doesn't really work anymore. So a better way to do it is to start actually applying threat intelligence at the DNS transaction to then do it, rather than just trying to shut yourself off from the world because it just doesn't work that way anymore. You can't really function. There are a few industries where I still see it, but it's pretty rare and it's definitely a really problematic way to set things up on an enterprise. I definitely wouldn't recommend it. If you don't have an internal root zone, don't even think about putting one end.
52:06 - Curt Franklin (Host)
We've had a lot of great information and, believe it or not, we've just barely scratched the surface on this topic. So we're going to be going into more depth, but before we do, we're going to hear one more time from Lou about a great quiet advertiser. Lou, take it away.
52:26 - Lou Maresca (Announcement)
Well, thank you guys. I'll get you back to your enterprise and IT News in just a moment, but before we do, we do have to thank another great sponsor of this week in Enterprise Tech, and that's our friends at ITProTV, who is now called ACI Learning. That's right 94% of all CIOs and CISOs agree that attracting and retaining talent is increasingly critical to their roles. But today's IT talent shortage is more important than ever. Your team skills need to be current. 87% of companies say they have skill gaps in their employees. The challenge of assessing your IT staff skills is really kind of overwhelming, but it doesn't really have to be.
53:01
Aci Learning now offers insights. It's a revolutionary skills gap analysis tool to assure you that the training you're providing is actually working, and a quick, one-hour assessment. Aci Learning's insights will allow you not just to see, but understand and fix the skill gaps on your IT team. This is the solution IT managers have been waiting for. With insights, identify specific skill gaps in your employees and see where your team's weaknesses lie. Empower your team with personalized training. Blanket training is really waste time and money. Insights offer detailed solutions, support and strategy by issuing recommendations and a training plan for individuals and your whole team. Compare results against other organizations so you know where you stand, and also test skills and close the gaps.
53:52
Practical labs that allow trainees to focus on the skills they need most. Aci Learning helps you retain your team and entrust them to thrive, while investing in the security of your business. More than 7200 hours of content are available, with new episodes added daily. Aci Learning's Stompsits competitors with a 50% higher completion rate. These are all the training solutions your business has been waiting for. Future-proof your team and company with insights from ACI Learning. Visit goacilearningcom. Twit listeners can receive up to 65% off an IT Pro Enterprise solution plan after completing their form. Based on your team's size, you'll receive a properly quoted discount tailored to your needs, and we thank ACI Learning for their support of this week in Enterprise Tech. Now back to you.
54:51 - Brian Chee (Host)
Well, remember how I said we DNS started off in a kinder, gentler world when we had a lot more trust. Well, with anything we can't. You know, there's a lot of people that do nasty things to us, and that's why we can't have nice things. So that's pushing us into a wonderful topic called encrypted DNS. Where does that fit in? Can I run encrypted DNS even if I'm a mom and pop store? Is it worth it? What kind of you know shenanigans do I have to go through to get it working in my enterprise?
55:32 - Josh Kuo (Guest)
Okay, we both have a lot to say on this topic, so I will start and then I'll pass the ball to Ross. So encrypted DNS is, as the name suggests, provides some level of privacy, and a lot of people get very excited. Oh, privacy, great. But like any encryption, it terminates. So if you're using, say, a cloudflare that has encrypted DNS, it terminates at 1.1.1.1.1. And from that point they can see every DNS query that you submitted, so they can, in a way, they're harvesting your DNS data. So that's first.
56:18
Privacy is a bit of a myth in our view, especially if you're using a third party provider. Now that it's bad, it's just like you need to be aware that this is happening at the far end. There's several flavors of encrypted DNS which we dive into in quite a bit of detail in our book. You can search for DNS in security on Amazon. It's probably the easiest way to find a book. We have a whole chapter dedicated to discussing the pros and cons of the different flavors of encrypted DNS. So the good news it has a place in the enterprise. We would say that it's inevitable. People are probably already using encrypted DNS without realizing they're using it. So from an enterprise point of view, then you should probably look into how to enable that from within on-prem or within your control, then rely on somebody else who's going to provide the service, echoing what Ross said, like an AAAAAAA.8, that you had no control over. And then Ross, I think, has quite a bit more to add.
57:35 - Ross Gibson (Guest)
So I think you pointed out the goal behind encrypted DNS is solving what was called the last mile problem and providing what a lot of people mistakenly think DNSSEC provides, which is privacy. A DNSSEC is a totally different technology and it functions to solve a totally different problem. And encrypted DNS, I think, for the home user I think generally is a good thing. Again, they're not trying to do anything on their DNS servers to where this is becoming problematic and you've got more and more browsers with it built in and turned on by default. You've got operating system makers doing it as well.
58:23
But in the enterprise world, if you're doing protective DNS internally, you're doing DNS security and your security team is trying to track DNS queries to perform some of their security analysis. That's where it actually becomes a problem, because it takes what otherwise would be visible data for administrators or security teams and now makes it encrypted and in some cases, makes it encrypted to a third party rather than your internal servers. So the key is that everybody's going to have to deal with is you're going to have to start running internal encrypted DNS servers to provide that service internally, so that those operating systems and browsers won't try to go out to a public service to get their encrypted DNS.
59:08 - Josh Kuo (Guest)
Right and then real quick. Add on to that in case it's not clear. In the enterprise that also means outbound and authorized DNS connection should never be allowed except from your own DNS servers. This will protect again, say some of you may remember. The DNS changer from, I think, almost 10 years ago, changes the DNS lookup setting. Actually I have that in the graphics that I sent over, the graphics that shows the. If we don't have it, it's okay. I think most of your listeners can see it in their head. The TCP IP setting under Windows right, you can set up your IP address and underneath that is the list of DNS servers to reach out to, in more or less in order preferred and alternate DNS servers.
01:00:01
Dns changer, worm changes that to go to whoever the attacker wants you to go to. So at the very minimum for the enterprise, you should not allow that to happen. No one should be able to go into their laptop or phone, change it to any DNS server they want to and talk to that DNS server on the internet. That really should be number one, don't let that happen. And number two, obviously, like what we said, implement protective DNS. So, even if your users try to go to a malicious destination. Your DNS server will stop that from happening.
01:00:44 - Ross Gibson (Guest)
And that's one of the twists of encrypted DNS is when you're dealing with traditional unencrypted DNS, stopping your users from using an external DNS server is pretty easy. On your firewall, you just block anything to TCP and UDP 53, and you don't have that issue anymore. If you're using DNS over TLS, which is one of the encrypted DNS technologies, it's also easy. It uses TCP 853, so you can block that port. The problem becomes much more complicated when you're dealing with DNS over HTTPS, which is typically known as DOE, because it's actually sending it over 443, just like all of your other web traffic. So there's no way to distinguish that traffic from any typical web traffic that you have going on, which was part of the design right in order to maintain that privacy. But in the enterprise space it creates a very large problem.
01:01:49 - Brian Chee (Host)
Well, you know we've had all kinds of topics. You know we're going on and on and on. But what if I don't want to run a DNS? Is DNS in the cloud actually safe?
01:02:05 - Ross Gibson (Guest)
Sure, yeah, I mean, if you're working with a reputable provider, you absolutely can get not just good security but great security. As you said and Kurt actually referred to earlier, particularly on the smaller side, it's hard to find and hire the expertise and in some cases it's a lot easier to contract with a firm that has people who have that expertise and can just provide you the service. Like you said, with the cloud for everything today, you know you've got Cisco doing it, you've got Infoblox providing it, you've got other providers Cloudflare you know that all have some type of protective DNS service. So there are a lot of great options out there from really reputable companies.
01:02:55 - Curt Franklin (Host)
Well, we have, believe it or not, pretty much filled an hour, and maybe our our cup runneth over a little bit, but fortunately we have more opportunities to talk about this. We'll be back next week with part two of this series. Before we get there, though, we want to ask our guests what we always ask our guests at the end of a show. Is there a place people can go to in order to find out more about Infoblox in general, and especially about the kind of DNS topics that we've been talking about?
01:03:32 - Ross Gibson (Guest)
So obviously, infobloxcom is a great resource with respect to that. They've got plenty of different. You know pieces there that talk you through all kinds of different offerings, including our protective DNS offerings, so that's a good. That's a good place to start if you're looking for particular solutions. If you're looking for something more generic and just learning about the topic, our book the Hidden Potential of DNS and Security is available on Amazon right now. As Josh mentioned before, if you just search for DNS in security on Amazon, it usually will come up and it's a completely vendor agnostic book. It's not Infoblox specific, it's totally generic, as far as you know. It's just straight DNS technology, dns threats, dns tax and not using one particular solution. So it's a great resource if you want to learn about this space and how you can use DNS as a security tool to help you know, secure your enterprise better.
01:04:33 - Josh Kuo (Guest)
Right and as we're getting updates, I think so far the best place is probably just follow Ross and I on LinkedIn. We are in the process of getting more information on our blog right now, just as a single entry, but when it has more we will yeah, we will make that available to the listeners.
01:04:58 - Curt Franklin (Host)
Wonderful. Well, we appreciate both Josh Kuo and Ross Gibson for being our guest today. As a matter of fact, we appreciate them so much. I think we'll have them on again next week. What do you think, Brian?
01:05:11 - Brian Chee (Host)
Yeah, I think so. In fact, why don't I give a pitch? Episode number two navigating external authoritative DNS for public domains. We're going to be talking about things like basics of domain name registration, design considerations for redundant external domain name for the public, and what is domain hijacking and how to guard against it. I'm looking forward to hearing about this. Learning about DNS is one of the things that I've been really meaning to do. It's on my checklist of things to learn and, gee, it didn't take much arm twisting with Josh to start lining up this deep dive. So, thank you, guys, appreciate this a lot and I definitely bought one of your books.
01:06:03 - Ross Gibson (Guest)
Well, thanks so much for that and thanks for having us on. This was a lot of fun.
01:06:07 - Josh Kuo (Guest)
Yeah, thank you, and we'll see you next week.
01:06:12 - Curt Franklin (Host)
Looking forward to that and we're looking forward to seeing each and every one of you next week as well. We are this week in Enterprise Tech. We are the authoritative source, not for your DNS information, except during these shows, but for everything you want to know about Enterprise Technology. And hey, don't forget about Club Twit. Add free content and access to our members only discord starting at just $7 a month. You can find out more about that at twittv slash club twit. And you can subscribe and download links to us at twittv forward slash twy it. Well, for all of us here at this week at Enterprise Tech, thanks for watching and remember, when it comes to Enterprise Technology, if you want to know all there is to know, just keep quiet.
01:07:22 - Jonathan Bennett (Announcement)
Hey, we should talk Linux. It's the operating system that runs the Internet, but your game consoles, cell phones and maybe even the machine on your desk. You already knew all that. What you may not know is that Twitter now is a show dedicated to it, the untitled Linux show. Whether you're a Linux pro, a burgeoning system man or just curious what the big deal is, you should join us on the Club Twit Discord every Saturday afternoon for news analysis and tips to sharpen your Linux skills, and then make sure you subscribe to the Club Twit exclusive untitled Linux show. Wait, you're not a Club Twit member yet. We'll go to twittv slash club twit and sign up. Hope to see you there.