Security Now 1075 transcript
Please be advised that this transcript is AI-generated and may not be word-for-word. Time codes refer to the approximate times in the ad-free version of the show.
Leo Laporte [00:00:00]:
It's time for Security Now. Steve Gibson is here. He's got some more thoughts on Project Mythos, the new super smart AI that can find security flaws. He's, he's saying, you know what, this isn't hype and he's got some real evidence behind it. We'll talk about Microsoft buying its own bugs back and ignoring other ones. And what, what do Steve think of Project Hail Mary? Yeah, even that. Coming up next on Security now,
TWiT.tv [00:00:34]:
podcasts you love from people you trust.
Leo Laporte [00:00:38]:
This is Twit. This is Security now with Steve Gibson. Episode 1075 recorded Tuesday, April 21, 2026. Yes, exactly. It's time for Security now.
Steve Gibson [00:00:55]:
Yay.
Leo Laporte [00:00:56]:
Tuesday has come. You've been waiting all week long to hear from this guy right here, Steve Gibson, the man in charge at Security Now. Hey Steve. Good afternoon to you, Leo.
Steve Gibson [00:01:06]:
Great to be with you again. As always. I got some feedback from the 20,000 plus listeners who joined my email list to receive the show notes. Yeah, as a consequence of my own schedule over the weekend, I needed to start work on this Friday. I finished Saturday afternoon and immediately sent out the show notes and the feedback was, wait, is it Sunday?
Leo Laporte [00:01:38]:
People are paying attention, Steve. You can't pull one over.
Steve Gibson [00:01:41]:
They're paying very close attention. Because I also, because I, my, my emailing system assumed that I would be doing the emailing in the morning of the podcast. It auto fills the day's date at the top of the email. But since I'm sending the mailing out typically on Sundays and occasionally on a Saturday, I have to go in and manual and remove the placeholder for the auto fill and replace it with the actual date. Unfortunately, something is wrong with me because this is not the first time I've put in 2024 as the year and so I sent it out as 4212020 24. And so several of our sharp eyed listeners said, don't think so.
Leo Laporte [00:02:31]:
Have we traveled in time and when?
Steve Gibson [00:02:33]:
Now I'm thinking I'm just going to leave it with Autofill and it'll date the email on the send date rather than the podcast date. Since you know that would work. Clever. Anyway, we're gonna have some fun. I, I hope that today's podcast will put to rest any question about what Mythos means, because two days after last Tuesday's podcast, the entire industry of security professionals, Bruce Schneier, who we know well, Google, ciso, I mean a who's who, all co signed and authored and produced a document that is intended to get the industry's attention because they all agree with me. So I titled today's podcast. Yes, exactly. Which is the name.
Leo Laporte [00:03:35]:
Yes. Yeah, exactly.
Steve Gibson [00:03:38]:
Yes, it is what I said last week. But we've got. I'd wanna, I wanna share just to really. Now this is probably at one point. Remember I said that last week's show notes was ver. Was revision three. In the first revision I wrote this could be the most significant podcast in our pod, in the, in the history of security. Now, now I, I got.
Steve Gibson [00:04:05]:
I, you know, did some deep breathing and in one of this follow on revisions I removed that sentence. But it, you know, my point was we're talking about potentially. Well then of course then my working name was Mythos Marketing or Mayhem because this could be a big deal. So.
Leo Laporte [00:04:26]:
Right.
Steve Gibson [00:04:26]:
Anyway, I just want to. We got a. An amazing document that I'm going to share. And the other thing that is useful is I've heard from some listeners who are having a hard time convincing upper management that, that they need to respond because of course any response is going to be expensive, right? I mean it's going to require expenditures of talent, equipment like, you know, upgrade, upheaval, whatever.
Leo Laporte [00:04:52]:
Well, that's why the flaws are still there in the first place.
Steve Gibson [00:04:56]:
Exactly. And of course. And then, and then there's the issue of the new things that haven't yet been found. So one of the things that this document offers, and in fact this is also the first time I've had two shortcuts and in one podcast for the same file. Because you can get to this two ways. GRC SC mythos or episode number GRC SC 1075. Because I want there to be no possible reason that our listeners can't get the PDF and send it up to the C suite, folks, because it is written for them. There are takeaways and bullet points and priority lists and this is what you have to do because a tsunami is very likely coming.
Steve Gibson [00:05:44]:
And in fact, I, I realize there's a. I'm already giving this away. I've got this whole thing in my head. It's. There's a very much of a Y2K aspect of this. Right? Think about it. You know everyone who said after, after we went into the year 2000, oh, look, that was nothing. Nothing happened.
Steve Gibson [00:06:04]:
Well, folks, there was a reason nothing happened. It's because everybody who needed to actually took it seriously and prevented something from happening. So anyway, we're gonna have, I think a great follow up today to last week's. That last week was just my opinion. Today we've Got everybody's opinion. But we're going to talk about a disgruntled developer who has been disclosing multiple Windows zero days because he's upset with Microsoft. Microsoft purchasing its own bugs in a massive campaign. The story behind something that's.
Steve Gibson [00:06:43]:
A couple of weeks ago, many of our listeners wrote to me. I didn't know what to say about it. I could have talked about it last week, but actually I bumped it because last week's podcast was full about how Veracrypt and Wireshark and some other projects suddenly lost their dev accounts at Microsoft. They were like, what happened?
Leo Laporte [00:07:03]:
We were.
Steve Gibson [00:07:04]:
They like, where they were unable to. To do revisions of their software for some reason. We now have the whole story there, which. So it's kind of good. I waited a week. So I, you know, because we were going to talk about it anyway. We got a serious problem of recaptured domain names, which is reminiscent of the bucket reuse that we talked about with AWS a couple weeks back. Also, a listener feedback inspired exploration of how exactly AI might help to secure.
Steve Gibson [00:07:40]:
Might best help to secure open source repositories. A listener wrote to say, hey, I never heard you and Leo talk about your opinions of Project Hail Mary. Could you say a few words? So we will. And then we're going to end with what cyber security professionals across the industry tell us about what Mythos means.
Leo Laporte [00:08:04]:
Oh, that'll be interesting.
Steve Gibson [00:08:06]:
And of course, again, the title of today's podcast is. Yes, exactly.
Leo Laporte [00:08:12]:
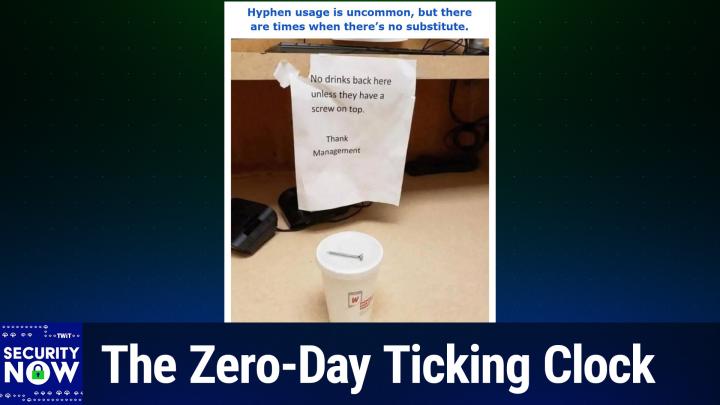
That gives you some idea of what's to come. Awesome. We also have a lovely picture of the week, which I haven't seen, but I know it's lovely because it always is fun.
Steve Gibson [00:08:23]:
This one. This one is a little. A bit of a hoot. So.
Leo Laporte [00:08:26]:
Yeah, a bit of a hoot coming.
Steve Gibson [00:08:28]:
A bit of a hoot.
Leo Laporte [00:08:30]:
All right. I am prepared to show all the.
Steve Gibson [00:08:33]:
Okay, so I gave this picture the caption. Hyphen usage is uncommon, but there are times when there's no substitute.
Leo Laporte [00:08:45]:
All right, I like the. I like the. This is going to be another punctuation.
Steve Gibson [00:08:51]:
Hyphen Usage is uncommon, but there are times when there's no substitute.
Leo Laporte [00:09:05]:
Okay, okay. Somebody took this quite literally. You want to describe it?
Steve Gibson [00:09:10]:
Yes, yes. So we have a. We have a sign. You can sort of see it. A keyboard on a shelf above and maybe a monitor. There's some sort of a. And there. And there's a power strip in the back.
Steve Gibson [00:09:21]:
There's some sort of a, you know, some sensitive electronics and, you know, PC stuff.
Leo Laporte [00:09:26]:
We had signs like this. All over our studio because I always bring my coffee in.
Steve Gibson [00:09:30]:
And yes, and the sign says no drinks back here unless they have a screw on top now. And then it says thank the management. Now they clearly meant a screw on top, not a screw on top. So what we have then is a styrofoam cup with one of those little plastic styrofoam lids and a long, about an inch and a half wood screw sitting on top of the cup. So it has a screw on top which all you, all you need.
Leo Laporte [00:10:06]:
It satisfies all requirements.
Steve Gibson [00:10:08]:
Yeah. Yes. And had it said screw hyphen on then it would have been clear that you didn't want a screw on the top of the cup. You wanted a screw on top Again. Punctuation container. Yes.
Leo Laporte [00:10:22]:
Can be very important.
Steve Gibson [00:10:24]:
Yes. Not many people use hyphens, but I like to hyphen.
Leo Laporte [00:10:28]:
I like hyphens.
Steve Gibson [00:10:29]:
Yeah, I do too. Yeah. Not quite clear when you need them, but I, I just say, hey, err, in the posit in this direction of hyphenating because what the hell. Okay.
Leo Laporte [00:10:39]:
We mentioned last time that the patch Tuesday last week was the second biggest patch Tuesday of all time. I mean, big numbers.
Steve Gibson [00:10:47]:
Yes. And we don't know yet whether that's mythos related, but we know that Microsoft is one of the companies that was named that anthropic gave, has given access to Mythos. So and, and you have to wonder because, you know, I've heard people talk about, oh, you know, like somebody was saying on some show, o you know, what do they think? There's no way that it's not going to escape, it's not going to get out. It's like they're not, you know, they're giving them access to the model online. They're not giving them mythos to go.
Leo Laporte [00:11:22]:
No, here's your mythos. We'll wrap it up for you to
Steve Gibson [00:11:27]:
wear it out or please make sure it's not like one of those iPhones it gets, that gets left at a bar when you, when you walk, you know, an unreleased iPhone. So anyway, there's no problem. But the fact that it's cloud based means that Microsoft would need to trust their competitor because of course they're all OpenAI. Whereas this is coming from Anthropic. They would need to trust Anthropic with their source code uploads into Anthropic's cloud in order to have mythos rummaging around in Microsoft source. So there's that. But then on the other hand, everybody is going to have to trust Anthropic in in that fashion because it's their cloud. There's no local mythos yet as far as I know.
Steve Gibson [00:12:12]:
Anyway, Last Thursday the 16th Bleeping Computers headline was New Microsoft Defender Red sun. That's the name of it. It's been given to it zero day proof of concept grants system privileges which as we know elevation of privilege is almost import as important as remote code execution because oftentimes the remote code that you're executing is in the context of a user login where the whole OS is has got security wrapped around the user to keep the user from misbehaving. So you need to first get into the user account but then you need to get out of the user account into the system account, you know, out, you know, into root. So as again you know, elevation of privilege is a big deal. So bleeping computers piece told the story of the disgruntled developer who had and I'll share some of what this guy wrote because we'll get. He sounds like he himself is a little more than disgruntled. He's a little sketchy but anyway this guy has been publishing not this is like not even the first fully working proof of concept exploit code for his discoveries plural of privilege of elevation vulnerabilities in both workstation and server like from like 2019 on it's like like server 2019 on have been vulnerable to this.
Steve Gibson [00:13:49]:
So the following day, on the 17th so on the 16th bleeping computers headline was New Microsoft Window Defender wet. You know zero day proof of concept grants system privileges. The next day they followed up that reporting with another piece titled recently leaked Windows 0 days now exploited in attacks. In other words, this guy put the proof of concepts up on GitHub and the next day bad guys had found them and were exploiting them to hurt Windows users. So not good. Bleeping computer said threat actors are exploiting three recently disclosed Windows security vulnerabilities in attacks to gain system or elevated administrator permissions. Since the start of the month, the security researcher known as Chaotic Eclipse or Nightmare. Oh, there's a hyphen nightmare nightmare hyphen eclipse.
Steve Gibson [00:14:50]:
So he's hyphenating. Has published proof of concept exploit code for all three security issues in protest to how Microsoft Security Response center you know, MSRC handled the disclosure process and we're not getting much much visibility into what that means exactly. Bleeping said two of the vulnerabilities dubbed Blue Hammer and Red sun are Microsoft Defender local privilege escalation flaws, while the third known as Undefend can be exploited as a standard user to block Microsoft Defender definition updates. At the time of the leak, the security flaws these exploits targeted were considered zero days by Microsoft's definition, which remember is little different than the industries since they had no official patches or updates to address them. Normally zero day is is about surprise. In this case it's about response essentially to a to something that hasn't yet been patched or updated, they said on Thursday. This is of last week Huntress Labs security researchers reported seeing all three zero day exploits deployed in the wild, meaning in use to hurt people. With the Blue Hammer vulnerability being exploited since April 10.
Steve Gibson [00:16:14]:
They also spotted Undefend and Red sun exploits on a Windows device that was breached using a compromised SL SSL VPN user in attacks showing evidence of what they're calling hands on keyboard threat actor activity, meaning not just automated scan stuff, but you know, an attacker logged in through an SSL VPN hitting keystrokes in order to explore and and exploit the vulnerable connection, they said. While Microsoft is tracking the Blue hammer vulnerability as CVE 202633825 and has patched it in April 2026 security update. So it got fixed last Tuesday, which was patch Tuesday of this month. They said attackers can use the Red sun exploit to gain system privileges on Windows 10, Windows 11 and Windows Server 2019 and later systems. When Windows Defender is enabled, it actually uses Defender in order to leverage its attack. So weirdly disabling Defender disables the zero day and they said even after applying the April patch Tuesday updates. So this is a, this is a vulnerability post patch Tuesday of this month. So we don't know when it's going to get fixed.
Steve Gibson [00:17:41]:
Maybe an emergency out of cycle update, who knows they said the disgruntled researcher explained. So this is the researcher saying quote when Windows Defender realizes that a malicious file has a cloud tag meaning you know like the remember the the mark of the web which tough tags are able to get saying we're going to treat this differently because you downloaded this off the Internet says when a malicious file has a cloud tag for this is the this is the the the disgruntled researcher writing quote for whatever stupid and hilarious reason, the antivirus that's supposed to protect decides if it would be a good idea to just rewrite the file it found to its original location. The proof of concept abuses this behavior to overwrite system files and gain administrative privilege unquote. And we'll we'll actually get a little more detail about that in a second. So they wrote. When Bleeping Computer contacted Microsoft earlier this week for more information on the disclosure reported by the anonymous researcher, a Microsoft spokesperson told Bleeping Computer, of course, isn't going to be as helpful as they generally are. Quote Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible. We also support Coordinated Vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community, unquote.
Steve Gibson [00:19:29]:
So thank you for that, Microsoft. So two days before that, on Wednesday, this person this is me talking now. This person going by the moniker Chaotic Eclipse posted his own diatribe over on Blogspot and I think it's worth sharing since it gives us some impression of who's doing the disgruntling. Dated Wednesday, April 15, the blog spot post was titled Public Disclosure. A response for CVE2026.338.25 patch so it reads, posted by the guy here is the code. Enjoy. And then he's got a GitHub link GitHub.com nightmare hyphen eclipse forward sl red sun. So he said now to so it looks like Nightmare Eclipse is the guy's name, right? And Red sun is the exploit.
Steve Gibson [00:20:25]:
Now to address what some media articles wrote. First of all, I want to talk about MSRC official response regarding Blue Hammer. That's his previous release of a zero day exploit proof of concept code. He said Microsoft has a customer commitment to investigated reported security issues and update impacted devices. Oh, so it's he. So so this is him quoting what what Bleeping computer just showed us they had they had said for what it's worth. So he said this is a very generic response, almost as if they don't care. And they don't.
Steve Gibson [00:21:09]:
Why? Because MSRC was fully aware of this public disclosure. A case was filed but was dismissed by them and they are also aware that this one will be disclosed. But again, they are ignorant. Period. This is again Mr. Disgruntled. Normally he writes, I would go through the process of begging them to fix a bug. But to summarize, I I was told personally by them that they will ruin my life.
Steve Gibson [00:21:39]:
And they did. And I'm not sure if I was the only person who had this horrible experience or a few people did, but I think most would just eat it and cut their losses. But for me, they took away everything. They mopped the floor with me and pulled every childish game they could. It was so bad duos on so bad. At some point I was wondering if I was dealing with a massive corporation or someone who is just having fun seeing me suffer. But it seems to be a collective decision. Wow.
Steve Gibson [00:22:14]:
And one I know. And one other thing, they do everything but support the research community. I won't disclose details, but they sabotage people a lot. I mean, just look at the past. Microsoft is the only major company who had a track of of multiple vulnerabilities being publicly disclosed just because the researchers were so upset by how MSRC treated them. Unfortunately, the folks who have the capacity to stop those disclosures not only don't care, but also seem to push harder for even worse exploits to be released. I didn't want to be evil, but they are actively poking me to start releasing rc, which I will be doing at some point. Dot dot dot.
Steve Gibson [00:23:03]:
He said he finishes. I will personally make sure that it go gets funnier every single time Microsoft releases a patch. Okay, so we talked about vulnerability discoverers feeling that their brilliance is not being sufficiently recognized or rewarded. In an earlier posting on March 26 last month, this person wrote, quote, I never wanted to reopen a blog and a new GitHub account to drop code, but someone violated our agreement and left me homeless with nothing. They knew this will happen and they still stabbed me in the back. Anyways, this is their decision, not mine. Unquote. Okay, so my presumption, without knowing anything specific, is that Microsoft almost certainly treated this researcher the same way they treat everyone else.
Steve Gibson [00:24:01]:
But he believed, or he or she believed that they deserved special treatment. You know, we've certainly shared horror stories in the past about the way some researchers have been treated, but Microsoft is not evil. It's full of good people, but, you know, a great many good people. So the result is that it's a big lumbering machine that doesn't care about anything. But, you know, only because caring is not what big lumbering machines are optimized to do. This researcher appears to have adopted, you know, and I didn't want to, but you made me do it. Rationale for his actions. Reading between the lines, my guess is maybe he was counting on receiving a big bug bounty payout that he desperately needed, which never came.
Steve Gibson [00:24:53]:
Sort of sounds like he may have released the proof of. Of. Of concept before Microsoft, you know, went through the. The formal disclosure process and so blew his opportunity because he pre released and so now he's complaining about that. So now of course he's blaming Microsoft for this. It's unfortunate that this person is having trouble with life. I looked at the details of the proof of concept that he designed and it's a slick bit of work. You know that the well known security researcher Will Dorman, from whom bleeping Computer often seeks confirmation of complex issues, posted about this new Red sun exploit over on Mastodon.
Steve Gibson [00:25:39]:
Will wrote from the same author as Blue Hammer. We now have Red sun. This works around 100% reliably to go from unprivileged user to System against Windows 11 and Windows Server 2019 and beyond with with April 2026 updates as well as Windows 10. As long as you have Windows Defender enabled, any system that has CLD API DLL should be affected okay, so CLD API sounds like the Cloud, the Windows Cloud API and is in the next quote from Will he refers to I car E I C A R. That's the abbreviation for the European Institute for Computer Antivirus Research. The file they produced, which itself is known as icar, is a popular pseudo malware test file that can be used to deliberately freak out any good AV tool without actually itself containing or doing anything malicious. It's just used as a as a test file to see if AV detects it. So he said in In a follow on Mastodon posting, Will writes this to explain what this thing does.
Steve Gibson [00:27:07]:
He says this exploit uses the Cloud Files API, writes ICAR to a file using it, meaning using the Cloud Files API, uses an opt lock to win a volume shadow copy race and uses a directory junction reparse point to redirect the file rewrite with new contents into C colon Backslash Windows Backslash System 32 Backslash Tiering Engine Service XE at this point the Cloud files infrastructure runs. The attacker planted Tiering engine Service xe which is the Red sun exploit itself as system and he writes game over. In other words, this is what this is the proof of concept that the disgruntled attacker developer engineered, which as I said is some slick work. I mean that's kind of tricky to figure that out. Anyway, our primary takeaway here is that all fully patched as of last week's Mega patch Tuesday. As you said, Leo, second biggest ever, but apparently not quite big enough. Windows Desktop and Server are currently vulnerable to this exploit, which is now being actively used in the wild. It's not the end of the world since something bad must first get into a machine so that it's able to trick Windows Defender into performing that odd file rewrite dance and that allows attacker provided code to be run with full system privilege.
Steve Gibson [00:28:57]:
But it's, you know, the attacker has to first get in there and provide the code. So as I said, while it's not the end of the world, Huntress Labs is observing it under active use. So it would be nice. Yeah. If Microsoft were to fix the issue for this before, you know, May's patch Tuesday, which is still a full three and a half weeks away. I mean this is a, this is a bad problem and you know, Microsoft didn't get there in time and they probably should get this updated in the meantime.
Leo Laporte [00:29:30]:
I think it's hilarious. Turn off Windows Defender.
Steve Gibson [00:29:33]:
Yes. Actually that is the only. That's the mitigation is turning turn off Defender because Defender is being used. This weird behavior that Defender has and I'm sure Microsoft knows why they're doing this but you know, it ends up you can leverage that in order to get yourself attacked. Yeah, I wouldn't turn off Windows Defender. I don't know what I would do. Maybe the zero patch guys, I'd haven't I didn't think to look over@zeropatch.com maybe they have a, a quickie patch and know they offer for free patches which Microsoft patches for vulnerabilities that are known but which Microsoft has not yet provided fixes. And they might do that.
Steve Gibson [00:30:16]:
So that, that might be an opportunity if, if they.
Leo Laporte [00:30:19]:
I'm checking right now just to see.
Steve Gibson [00:30:20]:
I'll let you know. Cool. Meanwhile, Microsoft has been buying up their own bugs. While we're on the topic of Microsoft and bugs, Bleeping Computer also reported that Microsoft has been breaking records for bug bounty payouts. And before I take note of the irony inherent in this, I'll share what Bleeping Computer wrote. They said Microsoft has awarded 2.3. Get this $2.3 million to security researchers after receiving nearly 700 submissions during this year's Zero Day Quest, which is the name of it, Zero Day Quest, you know, ZDQ hacking contest. Tom Gallagher, Vice president of engineering and Microsoft Security research center, that MSRC we were just talking about said that over 88.0of the flaws found during the live event at Microsoft's Redmond campus were high impact cloud and AI security vulnerabilities.
Steve Gibson [00:31:33]:
So that's just great. We've all been using that software which has 80 high impact cloud and security vulnerabilities. And actually Leo that may more account for Patch for the April patch Tuesday than Mythos stuff.
Leo Laporte [00:31:48]:
So you don't really need Mythos. There's plenty to go around.
Steve Gibson [00:31:51]:
Well just pay because $2.3 million. I mean what we've seen is this bug bounty concept paying. You need to motivate researchers who have, you know, only so many hours in the day to go running around chasing after Microsoft vulnerabilities. Although doesn't seem there's any that there's any scarcity of those, so bleepy computer continues Gallagher said. Quote during the 2026 hacking, the live hacking event, Microsoft partnered with the global security research community, representing more than 20 countries and a wide range of professional backgrounds, from high school students to college professors. Researchers conducted all testing within authorized environments in accordance with Microsoft's rules of engagement, demonstrating potential impact without accessing customer data or other tenant systems. Within these constraints, researchers identified critical paths involving credential exposure, ssrf, you know, server side request forgery chains and cross tenant access. So lots of cloud, lots of AI, he wrote or bleeping computer said.
Steve Gibson [00:33:06]:
Last August, Microsoft announced that it would increase the prize pool at this year's Zero Day Quest hacking contest to 5 million in bounties, which the company described as the largest hacking event in history. In 2025, Zero Day Quest also generated significant participation from the security community following Microsoft's offer of 4 million in rewards for vulnerabilities in cloud and AI products and platforms. So they they bumped it from last year's 4 million to this year's 5 million. After the hacking competition concluded, Microsoft announced it had paid 1.6 million in rewards after receiving more than 600 vulnerability submissions. So last year they offered 4 million. They paid out 1.6 after 600 vulnerability. This year they they offered 5 million and paid out 2.3 million. So lots more actual problems found.
Steve Gibson [00:34:11]:
The Zero Day Quest event contest is part of Microsoft Security Future Initiative, a cyber security engineering effort launched in November 2023 following a scathing report from the Cyber Safety Review board of the U.S. department of Homeland Security that found the company's security culture inadequate and required an overhaul. Of course we talked about this at the time. I mean they're it was just really raked him over the collection charging excess money for logging as an like logging security events so they could just turn it on. But it's like oh no, let's make some more money from having so many bugs that people have to log in order to track them right Anyway bleeping said. Last August, Gallagher said, quote, as part of our Secure Future initiative, we will transparently share critical vulnerabilities through the CVE program, even if no customer action is required. And here I hate this word. Learnings from the Zero Day Quest will be shared across Microsoft.
Steve Gibson [00:35:19]:
They're sharing their learnings.
Leo Laporte [00:35:21]:
They love that word I don't know
Steve Gibson [00:35:22]:
why, but God, you know, they. I mean, yeah, the things we learned. I think the things we learned is the way I learned my learnings. To help improve cloud and AI security in alignment with SFI's core principles, securing by default, by design and in operations. Apparently, however, not in code. Finally, earlier last August, Microsoft announced it had paid a record $17 million to 344 security researchers across 59 countries through its bug bounty program between July 2024 and June 2025. You know there's a mixed blessing, right, of bragging about how many millions of dollars you have paid to 344 security researchers who have found really bad problems with your software. On the one hand, okay, I think it's great that Microsoft software will now or will soon be that many bugs, fewer in cloud and AI security vulnerabilities.
Steve Gibson [00:36:32]:
That's, of course good for everyone. But as I said, it seems a little ironic to have Microsoft gleefully bragging about how many hundreds of bugs researchers were just able to find throughout their
Leo Laporte [00:36:43]:
products
Steve Gibson [00:36:45]:
when they were sufficiently motivated to do so. So anyway, as we know, none of those bugs should have been there in the first place to be found. But hey, Microsoft has way more cash on hand than it knows what to do with. So dangling increasing quantities of cold, hard cash in front of security researchers who will then be motivated to. To go bug hunting. That's definitely money well spent. Let's have more of it because Microsoft can certainly afford to pay. We're going to talk about the mysterious disappearing developer accounts, Leo, after you tell our listeners about one of our sponsors who's still here with us.
Steve Gibson [00:37:29]:
They've not mysteriously disappeared.
Leo Laporte [00:37:31]:
No, unlike those developer accounts. I just, I like the. What was it? Hands on keyboard. That's another good one.
Steve Gibson [00:37:38]:
Yeah, hands on keyboard attacker. Yeah, you can see like, oh, Boris is hunting. Boris is hunting and pecking.
Leo Laporte [00:37:46]:
Wow. Yes, wow. Recon 5 in our Discord says the term learnings was not in common use in 19th and 20th century. Although the countable noun sense learning, as in things learned, dates to Middle English and the plural learnings to early modern English. Note that early use of learnings often have the sense or connotation teachings. Yeah, I've heard teachings before. Yeah, as was the case of the of learn. Generally, it is found occasional use for centuries, including by Shakespeare.
Steve Gibson [00:38:19]:
So I think your instruction, if you're subject to teachings, what you come away with is learning learnings.
Leo Laporte [00:38:25]:
I don't like it either. I agree with you 100%. It feels like corporate speak.
Steve Gibson [00:38:29]:
It Feels like you've. What are you smoking on the peninsula? Steve, Steve, I think those little. Remember when they were there were all those fake sweepstakes sites.
Leo Laporte [00:38:42]:
That's another way. Yeah, we know that that happened on Facebook. That was the Cambridge Analytica scandal. They were making quizzes like which Star wars figure am I? And just by simply virtue of taking those quizzes, not only did they get all your Facebook information, they got all your friends Facebook information. So even if you said oh, I'm not going to do that, if your friends do it, they're revealing it. Yeah, now that hole's been plugged. But there's always more because they're like a cockroaches. You can't get rid of them.
Leo Laporte [00:39:13]:
All right, anyway, on we go. Let's talk about missing Microsofties.
Steve Gibson [00:39:17]:
One of the recent bits of news that that was, that was as I said, bumped so that we'd have time to thoroughly examine Anthropic's Mythos was that Micro last week was that Microsoft had without apparent cause or reason suddenly dropped a number of driver developer accounts products such as Veracrypt and wireguard. I mean like the, the well known Wireguard like next generation vpn. They both in. They inherently incorporate kernel driver components in order to obtain the deep OS level access they need in order to operate. So this was a huge concern for many users of these products. And I heard from many of our listeners who picked up on this news. Okay, as it turns out it was as I said before, it was just as well that I waited since last week, the news, the news, the only news that we had was that the accounts had been dropped. We didn't know why.
Steve Gibson [00:40:25]:
Today we know the reason for Microsoft suspension of these accounts turned out not to be a mistake but was entirely deliberate, which is also a process or a reason for some concern. And I know it probably is going to hit home for many of our listeners since it's an issue that I've been talking about recently during that whole process of updating my code signing certificate, what I had to go through, which, you know, like getting my CPA to sign an attestation letter that yes, he just laid eyes on me and I was real and he was putting his license on the line in order to vouch for me. It's like, yikes. None of that had ever been needed before. So once again, Bleeping Computer was on top of this. Under their heading Microsoft rolls out fast track to reinstate Windows hardware dev accounts. Kind of an oops. Anyway, Bleeping Computer explained writing Microsoft has rolled out a fast track response to help developers regain access to accounts recently suspended from its Windows hardware program following widespread complaints that they were locked out without warning.
Steve Gibson [00:41:46]:
Last week, the company suspended Windows hardware developer accounts used to publish Windows drivers and updates for widely used tools like WireGuard, VeraCrypt, MEM Test 86, Super Popular and Windscribe. The suspensions prevented developers from releasing new Windows builds and security patches, raising concerns about potential delays in responding to vulnerabilities. Veracrypt developer Manuri Idrasi stated that his account so this is Veracrypt, the successor to TrueCrypt, as we know, that was taken over by someone in France, this Adrasi guy. He said his account had been terminated without warning and that he was unable to reach a human support representative that leaving him unable to publish Windows updates. Similar experiences were reported by WireGuard maintainer Jason Donfeld and others who described being locked out without facing any or without access, or facing lengthy or unclear appeals processes. You know there was the machine, the Microsoft machine was just sort of ignoring them. After many developers took to X to report the suspensions, Microsoft Vice president Scott Hanselman said the accounts were suspended for failing to complete identity verification in the Windows hardware program and that the company had been emailing these people which they call partners about the requirement that since October of 2025. Right.
Steve Gibson [00:43:33]:
So six months of we're trying to reach you and you're not replying. Microsoft requires identity verification for the Windows hardware program because it allows developers to sign and distribute. Actually it doesn't anymore but okay remember Microsoft is doing the signing now and distribute kernel level drivers. It does allow developers to develop kernel kernel level drivers under the program which run writes bleeping computer with high privileges and had been well yeah in the kernel and have been like it could do anything have been abused by threat actors in past attacks. However they write many developers claimed and there's so many it's probably true claimed they had not received any prior notification including emails before they were suspended. While Hanselman and others at Microsoft have been working to reinstate accounts, Microsoft yesterday introduced a temporary process to fast track reinstatement for suspended accounts. An update to Microsoft's advisory adds quote We've heard your feedback. We know that some partners whose accounts were suspended by following account verification are experiencing challenges regaining access to the hardware dev center the HDC Protecting the security of Windows ecosystem remains our highest priority and we are adding a temporary process to accelerate the reinstatement experience for partners who are able to resolve outstanding compliance requirements wow.
Steve Gibson [00:45:20]:
Under the new process, developers are told they wrote to open a support case through the hardware program as the fastest way to reinstate accounts. Requests must include a clear business justification explaining how access to the hardware dev center will be used. Microsoft says that once reinstated, all outstanding compliance requirements must still be resolved before full access is restored. So this is sort of an interim. You know, we're, we're on a, on a provisional trial basis, we're going to give you your account back that you have had, you know, previously had access to for years until we decided, nope, no more. Suddenly we don't know who you are. But now you're going to have to tell us who you are and prove it. Of course.
Steve Gibson [00:46:11]:
Course. So Microsoft said it advised partners to ensure they're signed in with the correct account when submitting tickets and to continue prompting co pilot to create a ticket if automated assistance fails, whatever that means. For those unable to submit requests through standard channels, Microsoft provided an alternative support contact to help initiate the process. Microsoft has not said how long this accelerated process will remain in effect. That is what this grace period is going to be. So effective developers are advised to act quick, quickly. Okay, So I would tend to believe the developers over Microsoft regarding this complete lack of attempts to inform them. As I noted earlier, Microsoft is no longer an entity that is actually able to care.
Steve Gibson [00:47:10]:
Caring is not something that it does, it's just too big and caring is a distraction. So someone somewhere doubtless decided that the best way to get developer attention or just to remove dead accounts would be to simply suspend all currently non compliant accounts for non compliance. This has the advantage, as I said, of weeding out any older accounts that no one really cares about that much since they won't be immediately inconvenienced by their inability to access Microsoft's developer portal. And conversely, those who are inconvenienced will be highly motivated to get their identity proving act together. As we know, this may involving that this may involve getting an affiliated attorney or CPA to sign some attestation papers. It's what I went through basically this, it's the same process in order you need to have, you know, identity verification that is bulletproof. And of course that's, you know, that's true because running code in the Windows kernel is a privilege that no one, none of us want bad guys to have. So we do want Microsoft to make that as bulletproof as possible.
Steve Gibson [00:48:38]:
You know, while Microsoft could have been way more gentle about this, this did get the job done. So you know, that's what that was all about the reason Microsoft suddenly suspended a bunch of developer accounts, many that who were immediately inconvenienced because they were using them actively. Now, you know, basically it's like, okay, we're going to give them back to you for a while, but you need to get your identity made compliant. So that will happen. Okay, now this next piece of news beautifully exemplifies a problem we've, we've seen before that's I think largely a consequence of the aging Internet and aspects, critical aspects of its design that were never very well thought thought through since. And in defense of its designers, they could have never and never did foresee what their creation, which we call the Internet would become. They, I mean I'm in awe of the, the original design of these protocols that have stood the test of time. There are some aspects that haven't.
Steve Gibson [00:50:01]:
Bleeping computers headline for this reporting was quote, signed software abused to deploy antivirus killing scripts. Not a great headline. While that's factually true, it's more of the consequence of the problem than the problem itself. Okay, so but let's start with what bleeping computer reported. They said a digitally signed meaning, you know, there's a real company behind it. So it's digitally signed. And pretty much these days anything has to be a digitally signed adware tool. So not so not malware, not you know, not evil, but just unwanted.
Steve Gibson [00:50:44]:
And a digitally signed adware tool has deployed payloads running with system privileges that disabled antivirus protections on tens of thousands of endpoints, meaning host computers at where it was installed, some in the educational, utilities, government and healthcare sectors. In a single day, researchers observed more than 23500 infected hosts in across 124 countries trying to connect to the operator's infrastructure. With hundreds of infected endpoints being present in high value networks. Okay, so they're saying 23, 500 PCs have this adware tool. Hundreds of them are in like really important networks and they're all reaching out trying to phone home to this operator's infrastructure. Bleeping wrote security researchers at managed security company Huntress discovered the campaign on March 22 when signed executables viewed as potentially unwanted programs. Love that. Pups.
Steve Gibson [00:52:10]:
Pups potentially unwanted programs. Do you really want this? Which is what that, that original opt out tool that I wrote and for that old radiate or oriate mal, you know, adware was. Anyway, they said potentially unwanted programs triggered alerts in multiple managed environments. So Huntress is in the environment management business and they saw these things doing this. They wrote Pups or adware are regarded more as a nuisance than malicious, as their role is typically to generate revenue for the developer by showing advertisement popups, banners, or through browser redirects. You know, they'll, they'll. They'll infect browser URLs to bounce through some other redirect before they go to the site that you actually intend. Hunt researchers say that the software was signed by a company called Dragon Boss Solutions, llc.
Steve Gibson [00:53:11]:
Sounds kind of Chinese. Involved in quote, search, monetization, research, whatever that is activity and promoting various tools. For example, the Chrome Stera browser. Oh, Leo, don't leave home without the Chrome Stera browser. Chrominus, whatever that is. The. The World Wide Web. Oh, that's catchy Web genius.
Steve Gibson [00:53:39]:
And the artificious browser. I don't know if I want the artificial browser anyway. All labeled as browsers but detected as pups by multiple security solutions. So they're recognized as. Are you sure you want this? Beyond annoying users with ads and redirects, Huntress researchers say the browsers from Dragon Boss Solutions also feature an advanced update mechanism that deploys, and get this, an antivirus killer. In other words, they found out that there's things that don't like them, so let's kill that, because we don't want to be unliked. Huntress researchers discovered that the operation relied on the update mechanism from the commercial Advanced Installer authoring tool to Deploy MSI and PowerShell payloads. Analyzing the configuration file for the update process revealed several flags that made the operation completely silent.
Steve Gibson [00:54:41]:
You know, no user interaction required. You don't want to bother users with those pesky permission dialogues. It also installed the payloads with elevated system privileges, prevented users from disabling automatic updates, and checked frequently for new updates. So basically badly behaving malware. I would agree. Potentially unwanted, probably. Definitely unwanted. That would be dupe.
Steve Gibson [00:55:12]:
Definitely unwanted programs. Not a pup.
Leo Laporte [00:55:14]:
It's a dupe.
Steve Gibson [00:55:15]:
Yeah, that's right. Okay, so none of those things seem deliberately malicious. Right? Having been harassed by false positive AV detections, you know, I can at least understand their motivation behind creating exceptions for one's code. You know, as we know, that's not the approach I take. You know, like killing off av. That bothers you. Mostly. This seems like software written entirely with the convenience of its publisher rather than its user in mind.
Steve Gibson [00:55:51]:
That's bad software, no doubt about it, but that's also life. So the reporting continues saying, according to the researchers, the update process retrieves an MSI payload. You know, setup MSI disguise. This is weird. Disguised as a GIF image which is currently flagged as malicious on virus total but only 5 by only only by 5 out of 69 or 70 security vendors. So not many false positives or positive positives. Anyway, it does seem a little sketchy. Why would any software publisher who thinks of themselves as legitimate retrieve a Windows setup MSA file MSI file disguised as a GIF image? What? Okay.
Steve Gibson [00:56:44]:
Anyway, they continue writing the MSI payload includes several legitimate DLLs that that advanced installer uses for specific tasks, such as executing PowerShell scripts, looking for specific software on the system, or other custom actions defined in a separate file named exclamation point underscore string data that includes instructions for the installer. Huntress says that before deploying the main payload, the MSI installer conducts reconnaissance by checking the admin status, detecting virtual machines, verifying Internet connectivity, and querying the registry for installed antivirus products from Malwarebytes, Kaspersky, McAfee and ESET. The security products are disabled using a PowerShell script named Clock Removal PowerShell, which is placed in two locations. The researchers say that installers for the Opera, Chrome, Firefox and Edge browsers are also targeted, likely to avoid potential interference with the adware's browser hijacking. Yeah, you want to turn off anything that might get in the way. The clock removal PS1 script also executes a routine when the system boots and at logon and every 30 minutes to make sure that antivirus products are no longer present on the system by stopping services killing processes, deleting installation directories. Wow. You know, really wiping them and registry entries silently running vendors.
Steve Gibson [00:58:34]:
Uninstallers love that and forcefully deleting files when uninstallers fail to successfully uninstall. It also ensures that the security products cannot be reinstalled or updated by blocking the vendor's domains through modifying the hosts file and null routing them, redirecting them to 0000 wow. So again, not technically malicious, but you just don't want that. So what's clearly going on here is that the publishers of this definitely mal behaving crapware have previously experienced well deserved run ins with a handful of alert anti crapware utilities that want to warn their users that this is a potentially unwanted program in spades. So these cretins have upped the ante by making their adware offerings even more obnoxious in the things they do to get anything that doesn't like them off the system and keep them off. Like you can't even contact those AV companies any longer because you you the your browser will not resolve the domain because the hosts file has been edited in order to null route them. Wow. Okay.
Steve Gibson [01:00:05]:
So here's something curious and interesting. During the analysis, Huntress found that the operator did not register the main update domain Chrome stera browser Chrome sterabrowser.com or the fallback domain World Wide Web framework3.com used in the campaign. Presenting them with the opportunity Presenting them Huntress Huntress with the opportunity to sinkhole the connection from all effect infected hosts. In other words, domain got abandoned. Huntress saw nobody had re registered it so they did. As such, writes Bleeping Computer, they registered the main update domain and watched tens of thousands of compromised PCs reach out looking for instructions that in the wrong hands could have been anything based on the source IP addresses of the endpoints these PCs that are that are that have this crap on them. The researchers identified 324 infected hosts residing in high value networks. Remember, that's 324 out of 23,500.
Steve Gibson [01:01:33]:
So there's 23,500 PCs overall, 324 in high value networks, specifically 221 in academic institutions in North America, Europe and Asia, 41 OT, as we're calling them now, operational technology networks in the energy and transport sectors and at critical infrastructure providers 35 municipal governments, state agencies and public utilities, 24 primary and secondary educational institutions, three healthcare organizations, hospital systems and public health care providers and the networks of multiple Fortune 500 companies. So if a bad guy had registered that domain before Huntress did, they'd have access into all of those networks. Bleeping Computer wrote that they tried to reach out to Dragon Ball Solutions but could not find contact information as their site is no longer operational. Huntress warns that while the malicious tool currently uses an AV killer, the mechanism to introduce far more dangerous payloads into infected systems is in place and could be leveraged at any time to escalate the attacks. Additionally, since the main update domain was not registered, anyone could claim it and push arbitrary payloads to thousands of already infected machines with no security solutions protecting them by design and through an already established infrastructure. Huntress recommends that system admins look for WMI event subscriptions containing the string MB removal or MB setup, schedule tasks referencing WMI load or clock removal, and processes signed by Dragon Boss Solutions llc. Additionally, review the Hosts file for entries blocking AV vendor domains and check Microsoft Defender exclusions for suspicious paths such as D, Google, E, Microsoft or DD apps. Okay, so this is this particular incident is not the end of the world.
Steve Gibson [01:04:07]:
But as I noted at the start, it's another perfect example of something the Internet was never designed to handle. Some random company may itself not be explicitly evil, but might have sloppy, uncaring and abusive coders who install software that does things to its hosting PCs. That would raise serious concerns from anyone who understood what was going on. But as we know, the phrase from anyone who understood what was going on is almost never going to include the the end user who decided, hey, you know, I'll bet that Chrome Stera browser would be a lot better than Chrome, so I'm using Chrome Stera instead of Chrome. It's like, okay, so here's the problem. Yeah, so here's the problem that the Internet's designers never considered. What happens when the progenitors of ill begotten and very badly designed software, and not necessarily even that like any software which is now using an infrastructure to phone home to check for updates and then has the power to automatically download them and put them in place. What happens when that software, which continually reaches out to the Internet for updates eventually, and if it's a, you know, a fly by night company, probably inevitably goes out of business, their horrible software remains installed and alive and querying for updates.
Steve Gibson [01:05:59]:
I know that all of us have stuff on our PCs that we installed some time ago and then stop using, but probably haven't taken the time to remove because it's not bothering us. But then their various domains also expire.
Leo Laporte [01:06:15]:
Oops.
Steve Gibson [01:06:17]:
Now anybody could re register them. Fortunately in this instance Huntress are the good guys who re registered those expired domains for the sake of their research. But if bad guys were to do this, they would have stumbled upon the mother lode. 221 academic institutions, 41 operational technology networks and infrastructure providers, 35 municipal governments, state agencies and public utilities, 24 school systems, three healthcare organizations and the networks of multiple Fortune 500 companies they could get into. All of them. Ransomware, anyone. This abandoned software would literally have a ready to go back door into the networks of all of those 324 high value targets. And here's the concern to think about.
Steve Gibson [01:07:15]:
This cannot be an isolated event. This particular discovery was Huntress showing that they're awake and alert and and doing their managed security thing. That's great. But similar events are doubtless happening across the Internet. Companies are abandoning their previous failed software offerings, which included technology to phone home. Then home is abandoned too. Note that it's one thing when some random website's domain is abandoned, but it's an entirely different matter when Automation that's been silently installed into user machines is making those queries. This creates a ready made backdoor into every one of the networks that's reaching out to abandoned domains.
Steve Gibson [01:08:14]:
We're in a world where there is no accountability for the actions of the software while it's in use. Right. I mean people can download this crapware and it does that to their machines. Horrible things. Installing scheduled tasks, stripping AV out, running the AV uninstallers and if that doesn't work, removing their registry entries and manually deleting the software for their machines. Black holing their domains by putting 0.0.0.0 in the hosts file and the user doesn't know. They, they said yeah, I really want the Chrome Stere browser. Sounds great.
Steve Gibson [01:08:56]:
And this happens. There's no accountability in our current environment. Companies can do whatever they want, including this kind of crap. You know, you know this. Basically we're in a world where we have a rent a domain name system. Right. We rent a domain name and, and as long as we're willing to pay for it, we get to keep it. But when we decide we don't want to rent that domain name any longer after it expires, it's up for grabs.
Steve Gibson [01:09:26]:
Just like the AWS abandoned bucket problem was where bad guys could grab abandoned buckets that were, you know, still had activity on them. So unfortunately this re registering a domain is assumed and encouraged, but it leaves us with some serious potential for security problems. It's not something our forefathers on the Internet thought about because they could have never imagined that the net would become what it has. But this, this problem of recycling domains, it creates a whole new world of security problems.
Leo Laporte [01:10:05]:
What an interesting story.
Steve Gibson [01:10:06]:
Yeah.
Leo Laporte [01:10:08]:
From Stera. I can't wait to get it. By the way, I just saw this news cross the wire.
Steve Gibson [01:10:15]:
Yeah.
Leo Laporte [01:10:15]:
Mozilla is saying now that it used Mythos on Firefox and that it found 271 bugs which they patched in their current version, 150. So this is the first that we've seen of an actual admission that Mythos was used and by an independent third party. 271 bugs in shipping software that's been tested and tested and tested.
Steve Gibson [01:10:48]:
Oh my God. Pounded on. And we know it is the largest attack surface on anyone's computer is the web browser. Yeah.
Leo Laporte [01:11:00]:
One of the things Mozilla said is this is our belief is that the tools have changed dramatically and there were categories of bugs you couldn't find that you could find with human analysis. You couldn't find with automated analysis, which means that threat actors had an advantage if they were willing to spend the time and energy we couldn't keep up.
Steve Gibson [01:11:22]:
And now it is finding them with automated analysis.
Leo Laporte [01:11:26]:
Every piece of software. This is, by the way, this is Holly Bobby, Holly, Firefox's cto. Every piece of software is going to have to make this transition because every piece of software has a lot of bugs buried underneath the surface that are now discoverable. This is a transitory moment that is difficult and requires coordinated focus and a lot of grit to get through. But I think that this is a finite moment. Even as the models become more advanced. He said, yes, we are flooded now with things we have to fix, but at least we know about them. Yeah.
Steve Gibson [01:12:01]:
And when AI is in the pre delivery pipeline, we're not going to be there again. So as I said, we are going to have. It's transient mayhem, potentially. It's Y2K. This Y2K is a perfect model.
Leo Laporte [01:12:16]:
I think this confirms what you just said. Exactly. Yep. It is Y2K. It's hair on fire. But for a limited time only.
Steve Gibson [01:12:25]:
Yes. Now. And. And you know that going forward, have with fire. With the Mozilla team having seen this, they will vet anything they do now through AI to cat to as a like hyperlint in order to catch any. Any of the problems before they ship.
Leo Laporte [01:12:44]:
That's what Holly is saying basically is this is now incumbent on everybody.
Steve Gibson [01:12:48]:
This is the new model.
Leo Laporte [01:12:49]:
It's a new model. It's a future. But this is a real confirmation that Mythos wasn't merely marketing hype, that there is something going on. If you can find 271 bugs in a highly tested version, current version, please
Steve Gibson [01:13:06]:
tell Jeff and Paris. I'm so annoyed with. They're like, is it really? Yes. Read something.
Leo Laporte [01:13:13]:
It is now. Well, we didn't. I mean, to be fair, we did. We weren't sure. Sure. You know, because. Yeah, you said that last week.
Steve Gibson [01:13:22]:
Yeah, yeah.
Leo Laporte [01:13:24]:
And I mentioned that to them. But now we. Now we have absolute confirmation. This is. This is the real deal. Because they've been using automated tools before. This is not.
Steve Gibson [01:13:35]:
It's.
Leo Laporte [01:13:35]:
This is a special category.
Steve Gibson [01:13:37]:
And I will. When we get to our main topic. I will. The. The guys at Aisle. Remember. Remember Aisle. The.
Steve Gibson [01:13:45]:
They're the guys that found all the problems in open ssl and so they have a little bit of pushback against Anthropic, which I'll share.
Leo Laporte [01:13:52]:
Okay.
Steve Gibson [01:13:53]:
To round this out. But anyway, as I said, the podcast is titled. Yes, exactly.
Leo Laporte [01:14:01]:
Exactly. And you were. You called it. You were absolutely right. We've got some feedback. What? Oh, you're muted. Hello.
Steve Gibson [01:14:14]:
Thank you. Okay, so feedback. A listener shared some musings over strategies for securing open source repositories, and it provided a perfect setup for an ASP for looking at this aspect of the future. So his name is Gene Hastings and who listens to us. I'm familiar with the name. He sent email in the past, he wrote. A colleague and I often meet to talk about DevOps and related issues, you know, system and personal health. He's more dev, I'm more ops.
Steve Gibson [01:14:49]:
Both often cranky one of our listeners in any event, we were talking about the nightmare that's having a project's dependence on libraries all over the net and what steps might be taken to provide some degree of defense, he said. I was already aware of version pinning and there was the recent news about a compromised package where the infection modified it without changing the version. I recalled long after our conversation that one would need to store a hash of the package and compare it on retrieval right, because then a modification will get detected that would the hashes would match, he said. Little protection against a compromised new version of or a first time use, but some nonetheless. There's also the concern as to the trustworthiness of the package's own dependencies. All this led me to reflect that what may need to happen next is having is to have each package and its components not only signed by the author, but also by an independent auditor. Obviously the this does not scale physically or financially, so the next step is to have a trusted agenic auditor that does not charge a fortune for each signing. Such automation will be necessary soon.
Steve Gibson [01:16:11]:
This led me to a further thought. Imagine a new project philosophically akin to let's encrypt a service for smaller developers who can do an automatic audit at a tolerable expense. He says if all of the following are true, the agents like Mythos and descendants are competent, the agents are efficient, the agents are trustworthy, the agents are not priced out of reach with some flavor for everyone and the owners of the agents are trustworthy. He has an exclamation point on that one. He said then there could be a future for us and the Internet, apparently otherwise, forget about it, it's all over, he said. As an aside, I am an AI skeptic. I do not trust that which cannot be explained. Getting back to operations, if I don't have a half decent idea what a system and its configuration is doing, I am very reluctant to put my name on it.
Steve Gibson [01:17:11]:
I am willing to trust people who are able to understand the systems to assure me that I can be fairly reassured. At the moment, such people are hard to find amid the tsunami of hype. I'm also, I'm, I'm not as concerned about the quality of the technologies. I am about the people pushing them. I wouldn't trust simple driving directions from the likes of Sam Altman, Mark Zuckerberg or Jeff Bezos. I do not trust their motives, plans or motives or plans. Signed Gene Hastings. Okay, so thank you.
Steve Gibson [01:17:45]:
As he said, often cranky, cranky Gene, he's suggesting a future, a future solution which might be a system in the form of let's encrypt where individual developers would need to have an AI based agent audit their code for problems and, you know, unsuspected or unwanted behaviors and would then sign the library all for a low cost. The trouble with this is that then we need some authority to manage the trust in these AI agent signatures and on the trusting end, some sort of new root store that users of these signed libraries could use to look up and verify the trust. In other words, a whole bunch of new stuff. I think there's a more direct, cleaner and straightforward means of accomplishing the same thing. We simply move to a world very much like what we were just talking about Leo with Mozilla. We move to a world where anything that a public code repository offers for broad public consumption first passes the scrutiny of an AI agent. An AI will be guarding the exits essentially. Code cannot leave the repository without first being checked by the AI agent and the process might not be autonomous.
Steve Gibson [01:19:24]:
You know, the, the repository's AI might have some questions for a package's authors that would need to be answered and negotiated before a new or updated package could be made widely available. And since the use of an AI will certainly come at a non zero cost for the foreseeable future at least they'll probably always be some cost because this is always going to be some compute. I'd imagine that there would be some form of rate limiting on submission, new submissions being made available publicly for, for review and publishing. You know, non professional authors who are in the habit of constantly revising their code to know, to make an endless series of incremental improvements might have a release delay or some sort of submission limit imposed. But, but the idea being in the same way that Mozilla will be running their Firefox code from head from now on through AI, the solution is for repositories to do the same thing to clean anything that is being released to the public before it gets out there. And I suspect that solves this problem. You know, the vast majority of a repository's code is mostly static, right? So an AI would only need to give it the once over one time, and from then on, those who pull it could rely upon its security more than they ever have been able to before. And most code only changes incrementally.
Steve Gibson [01:21:06]:
So an AI could retain the context that it developed during that original once over and then bring itself back up to speed and only look at the changes, all the deltas to the code order to minimize the recurring cost of continuing to review code which incrementally changes over time. So I think the whole system can be made practical. So what I know is this, you know, the year is currently 2026. See, I got it right this time. It's not 2024, 2026, when AI costs today far more to run than it's able to generate in revenue. I am sure that the economics of AI will be radically different in the future. Just as the economics, for example, of mass storage and computation have been utterly transformed over the past 50 years.
Leo Laporte [01:22:09]:
There's a rich history of this. This has always happened.
Steve Gibson [01:22:12]:
Today we're all walking around with globally connected pocket computers that would have boggled the minds of our grandparents.
Leo Laporte [01:22:20]:
Yeah. So our parents forget the grandparents. Yeah.
Steve Gibson [01:22:25]:
It should be clear to everyone that AI which continues to boggle our minds today will be just as accepted and taken for granted by our grandkids as the Internet is by today's kids. So, you know, I mean, you know, kids growing up today, they've always had the Internet. That's just like, yeah, they don't know life without it. We're still sort of like, wow, remember those days? Remember books used to remember. That's right. DVDs, records. And finally, GP our listener says. Dear Steven Leo, Given April's security related news, I can see how thoughts on the project Hail Mary movie might have been pushed to the wayside.
Steve Gibson [01:23:08]:
I'm wondering what you gentlemen thought of the film and its treatment of the source material. I felt the movie struck a nice balance. It did justice to the book while allowing those who have not read it to enjoy the story without being overwhelmed by a flood of science which could have easily turned it into a five part miniseries. Oh yeah, he said a lot of
Leo Laporte [01:23:30]:
science in the book.
Steve Gibson [01:23:31]:
Yeah, there is. Well, and that's why we love Andy Weir's writing.
Leo Laporte [01:23:34]:
Right.
Steve Gibson [01:23:35]:
So he said, my young one enjoyed the movie so much that the young ones. Oh, young one that they. They that they wanted to read the book. So.
Leo Laporte [01:23:47]:
Good.
Steve Gibson [01:23:47]:
So we.
Leo Laporte [01:23:47]:
Yeah, that's good.
Steve Gibson [01:23:49]:
Yes. So we signed up to borrow it from the library. However, we were number 110 in the queue of the public library to. To borrow the book. Yeah.
Leo Laporte [01:24:01]:
So we saw the best seller list again, I think.
Steve Gibson [01:24:03]:
Yeah. Yeah. So we opted for my old copy on Audible instead list. Although I salute him for reading because I'm still a. You know, I think reading is. Is primal. But anyway, he said listening to the story again did not diminish the movie. It only enhanced the experience for both me and my little one.
Steve Gibson [01:24:22]:
It's like getting the inside story, if you get my drift. This is one of the few times in recent history where a movie did not ruin the book, but. But actually improved upon it. Good job to the production team on this one. All the best. GP so, Leo.
Leo Laporte [01:24:39]:
Yeah, I'd agree 100%. In fact, I'm re listening to the book, which I started right after the movie. The other thing we did do, though, is we also rewatched the Martian because Lisa and I had a little inside bet, because after the project Hail Mary, I said, oh, that was as good as the Martian. She said, no, it wasn't. And she said, it was really good, but it's not as good as the Martian. And I said, oh. And then we watched the Martian, and I have to agree with it, the Martian was remarkably good.
Steve Gibson [01:25:05]:
Yeah.
Leo Laporte [01:25:06]:
I think that's partly because Ridley Scott directed it. I think the directors of Project Hail Mary, who chiefly are famous for the Lego Movie, maybe have a little bit more of a kiddie sensibility. I could see I would appeal to his little ones because, you know, Grayson is Grace Ryland. Grace is like. There's a lot of times he goes, oh, you know, things that kids would like. Yeah, but it's a little over the top. That bugged me a little. I do feel it was very true to the book.
Leo Laporte [01:25:37]:
The book has infinitely more detail.
Steve Gibson [01:25:40]:
Yes.
Leo Laporte [01:25:40]:
Because you had to cut all that stuff out. I'd forgotten how much science there is in the book. And so there's stuff that I thought, oh, boy, they.
Steve Gibson [01:25:49]:
They didn't.
Leo Laporte [01:25:50]:
They left that part out of the movie.
Steve Gibson [01:25:51]:
But, for example, I loved the details of breeding astrophage from the book. It was so good.
Leo Laporte [01:25:59]:
Right.
Steve Gibson [01:25:59]:
And we just got a little. A little suggestion of it in. In. In the movie, almost all the science
Leo Laporte [01:26:04]:
is suggested, you know, in the movie.
Steve Gibson [01:26:07]:
Yeah, yeah.
Leo Laporte [01:26:08]:
They focus on the drama, the interpersonal relationships, and so the science gets a second.
Steve Gibson [01:26:14]:
So my theory, because I've. You know, I've reread the book when we knew there was going to be a movie, because I read it originally when Andy wrote it, and I thought about this question of movie versus book a lot. Of course, famously, I've complained here that. That. That Jurassic park, the. When I was watching the movie, I was incensed because so much was left out that was in. I mean, some arguably really important stuff. On the other hand, look, Jurassic park was a phenomenon as a movie, so who can say that? Like, there's.
Steve Gibson [01:26:53]:
What I've decided is. It's really not fair to compare. Yes, they are two. What they have in common is a similar plot. So. So they have the concept and the plot, but you really are addressing two different audiences. A book reader or audible listener is a different audience than somebody who wants to go to a movie in two hours and be entertained.
Leo Laporte [01:27:18]:
They're different media. Yes, absolutely. And you have to be native to the medium, otherwise it just isn't going to work. And I understand that. But I do agree with you that this. Which is unusual, and our correspondent, this movie makes you want to read the book, which is really great. And you don't feel. Feel disappointed in either direction, which is very unusual.
Leo Laporte [01:27:40]:
I almost always feel disappointed by science fiction books not living up to the movie. In this case, no. I think for both the Martian and Project Hail Mary, the movies are great. They really do a good job. Yeah. So we're in agreement.
Steve Gibson [01:27:55]:
Yeah. Okay, let's take a break and then we're going to plow into what the experts say and what you. You just shared a perfect example from Mozilla what they found when they ran Mythos against their Firefox code base.
Leo Laporte [01:28:11]:
Yeah. Yeah, very interesting. I. I do have to point out Redcon5 asked in the Discord chat, our club Twitch chat, how many of the 271 bugs were severe or were. You know, and they actually didn't talk about severity, so I don't know. They might have been smaller bugs. I. We don't know.
Leo Laporte [01:28:31]:
So that's the next question. But I guess a bug is a bug is a bug.
Steve Gibson [01:28:34]:
I mean, and we know how often bugs can be elevated into something more severe, right?
Leo Laporte [01:28:43]:
15 of the Firefox CVEs were low, 18 were moderate, 13 were high. least of those. At least. That's according to Joke and Boken. So on the YouTube.
Steve Gibson [01:28:54]:
And I realized that the proper response to the guy in the club is, listen to what the Mozilla guy is saying.
Leo Laporte [01:29:02]:
Yeah.
Steve Gibson [01:29:03]:
He is saying, gotta do. This is significant. Yeah. You Know, this wasn't. This wasn't dust that was found. Yeah. You know, they were like, whoa. So.
Leo Laporte [01:29:13]:
And that number is huge. 271 is mind boggling. But. But if 13 were high, this is from version 149 to 150. This is. This is huge.
Steve Gibson [01:29:26]:
Yeah.
Leo Laporte [01:29:26]:
Anyway, let's talk about it.
Steve Gibson [01:29:28]:
And just one package. We're talking about the. I mean, all. Think of all the software in the industry. Think of, Think of how. How minutely Firefox has been curated and, and developed over time, how much scrutiny it's received. And even so, AI found what people could not. Now imagine the typical software that's just thrown together and out the door.
Leo Laporte [01:29:57]:
Think about Windows, how many hundreds of millions of lines of code.
Steve Gibson [01:30:01]:
Well. And how many bugs they know about and don't like. Eh. Remember, didn't they ship famously seven with like 10,000 or 20,000, like known bugs? Like what. How does it even get off the ground?
Leo Laporte [01:30:15]:
Oh my gosh.
Steve Gibson [01:30:16]:
Yeah. It's a revolution. Okay, so.
Leo Laporte [01:30:19]:
Exactly. Steve.
Steve Gibson [01:30:21]:
Yeah. As I noted several times last week, my original working title for last week's podcast was Mythos. Marketing or Mayhem? But once I'd assembled and examined all the data, I realized that leaving the question to the, you know, leaving the question or the answer to the question that that title implied up in the air would be wrong. Because there's no way, really, after looking at the facts and just with no bias, there's no way that Mythos was only marketing. We had evidence of it. So, you know, I acknowledged also that it was certainly also marketing, but it was also far more than only that. And I think that's where people get confused, is they just mistrust people's motives to such a degree these days that it's like, oh, but. But again, it could be both.
Steve Gibson [01:31:17]:
And it was. It happens at Anthropic. Use this for marketing. But I'm going to make the point at the end of the podcast. Thank God. Because it broke out. That's the difference. And that this breakout is what we're talking about today.
Steve Gibson [01:31:35]:
I titled today's podcast. Yes, exactly. Because last Thursday, two days after, as I said at the top of the show, two days after our what Mythos means podcast was delivered, an incredibly significant group of industry veterans who pretty much comprise a who's who of the cybersecurity industry, all weighed in with a formal emergency wake up call for the entire cybersecurity world. The organizer and publisher was a group calling themselves the Cloud Security Alliance. And I have a link to the most Recent version of their 23 page paper. In the show notes, they titled it the AI Vulnerability Storm Building a Mythos Ready Security Program. So the paper enumerates its 16 primary contributing authors. Because this is important for appreciating the weight of the paper's stated concerns, I'm going to share them briefly.
Steve Gibson [01:32:44]:
They are Jen Easterly, CEO of the RSA Conference and former director of cisa. Bruce Schneier, who we all know, renowned cryptographer, current head or chief of Security architecture and at inrupt and fellow and lecturer at the Harvard Kennedy School. Chris Inglis, the White House's former National Cyber Director. Phil Venables, Ballistic Ventures formal. He is formerly the CISO of Google Cloud. Heather Adkins, current CISO of Google Rob Joyce, the NSA's former cybersecurity director. Sunil Yu, the CTO of Gnostic and former chief security Scientist for Bank of America. Katie Mazouris, the founder and CEO of Lutta Security.
Steve Gibson [01:33:36]:
John N. Stewart, Talens Venture and former CSTO for Cisco. James Line, CEO of the SANS Security Institute. Dave Lewis, Global Advisory CISO for 1Password. Maxim Kowalski, Managing Director of AI Security CoE for Consortium Networks. Jim Reavis and John yo, who are the CEO and cso respectively of that cloud security alliance. Joshua Sack, CTO and co founder at Security Superintelligence Labs, former AI and llama security head at Meta and finally, Rami Husani, CCSO for none other than cloudflare. So in it.
Steve Gibson [01:34:25]:
So as I said, the who's who, in addition to those primary contributing authors, the paper's content was also reviewed by a list of CISOs that pretty much includes everyone else. I'm not going to read them since there are too many of them, but I reproduced that page from the report in the show notes so you can just see it. I mean, it is like there's anybody who I didn't just read. A former head of security for Netflix, CISO for Brave Technology. You know, I mean, uh, uh, global field CISO for fastly, you know, your eye just drops on any of them. I mean, so you know, everybody basically understood what Mythos meant. Okay, so we've clearly established the provenance of this document, so I want to first share the executive summary overview, then the key takeaways for CISOs, followed by their brief summary of why Mythos is so important. Much of this will sound exactly like I did last week, two days before this was published.
Steve Gibson [01:35:43]:
Which is of course why I immodestly titled today's podcast. Yes, exactly. This amazing group of experts, even use some of the same phrases that I used. Given the impossible to exaggerate significance of Mythos and the successor systems that are sure to follow. And and not only philanthropic, but I get it. As I said last week, they're just first, but they were the one that broke through. And breaking through is what we really needed for our industry to get the wakeup call it needs. So I think it's crucial for the listeners of this podcast to appreciate that it's not just me with a lone opinion here.
Steve Gibson [01:36:26]:
Okay, so the authors of the executive summary set it up as a sort of topical Q and A. They wrote, what happened answered AI as demonstrated by Anthropics Mythos. So again noted that even they didn't didn't, you know, fall, you know, to their knees in front of Mythos. They're saying, AI as demonstrated by Anthropics Mythos has significantly increased the likelihood of of attackers discovering new vulnerabilities, creating new exploits and using them in complex automated attacks at scale. While AI also increases the speed of patch development and reduces defects in new software, defenders still face a heavier relative burden due to the inherent limitations of patching, attackers gain asymmetric benefits. And that's what I referred to last week when I was talking about the existing installed base of software that hasn't had the opportunity to be screened through AI. It's already deployed, it's in devices and appliances, and many of it has been forgotten, but not by the attackers who want to use it to get in. So they asked the question, how is this different from the status quo? And answered in the near term, security organizations will likely be overwhelmed by the need to apply patches and respond to AI discovered vulnerabilities, exploits and autonomous attacks.
Steve Gibson [01:38:14]:
What to do now to deal with the current risk spike? Adjust risk calculations and reorient security program resources for increasing volume of patches, decreasing time to patch, and more persistent and complex attacks. Focus on the basics and harden your environment further. Segmentation, egress, filtering, multi factor authentication, and defense in depth breadth all increase the difficulty for attackers. What do we believe will happen next? The storm of vulnerability disclosures from Project Glasswing is the first of many large waves of AI discovered vulnerabilities that may occur in rapid sequence. The capabilities seen in Mythos will quickly become more widely available, dramatically increasing the number and frequency of complex novel attacks organizations will face. And finally, what else should start now to be should start now to be ready for the next waves. Prioritize robust dependency management to reduce vulnerabilities in third party and open source components. Enforce automated security assessments consistently in your development process, including using LLM powered agents to find vulnerabilities before attackers do.
Steve Gibson [01:39:50]:
Introduce AI agents to the cyber workforce across the board, enabling defenders to match attackers speed and begin closing the gap. Reevaluate your risk tolerance for operational downtime caused by vulnerability remediation to account for shorter adversary timelines. Update governance for more efficient vendor onboarding and increase headcount to facilitate a faster cycle deployment of new AI based defenses. As an industry, we need to strengthen our coalition's cooperation and coordination okay, so I think it should be clear from these executive summary bullet points that the cybersecurity industry's posture on Mythos is that there is less than no time to waste. This is not the time to adopt a wait and see posture and to be reactive to events. By the time a reaction is indicated, it will be too late. Despite these clear alarms being rough run by many, security being rung, the alarms being rung by many security professionals who have no profit stake in any of this being true, inertia being what it is, many organizations will nevertheless wait to see if anything really happens. For what it's worth, I did not wait.
Steve Gibson [01:41:23]:
Although GRC's border security has always been as strong as I've been able to make it, as I've mentioned before, I did have two deliberately exposed SSH servers listening for connections from any US domestic IP foreign IPs have always been hard blocked. I'm referring to them now in the past tense because after Mythos they're already shut down. I've used those SSH links to allow me to deal with the rare IP changes in my two Cox cable connections. An SSH session allows me to update the firewall filters that block all other connections from anywhere other than my two remote work locations. Even though those SSH servers are both using the strongest multi factor identity authentication available. That might not matter if some bypass vulnerability is found. I don't need those SSH servers as much as I need security. So I'm going to take a wait and see approach in the opposite direction rather than waiting to see whether a problem is found and then hoping I get the news quickly enough.
Steve Gibson [01:42:45]:
I'm going to assume that someone using Mythos might discover something unforeseen in the SSH server software I'm using. So I'm going to wait and see about that before I feel safe to poke my head out again. And in fact I may drop SSH completely with its inherently open ports altogether and come up with an affirmatively more secure solution Leo like you were talking about using tail scale in order to get into your your inside because tail scale is able to do NAT penetration, in which case you don't have to have any open ports.
Leo Laporte [01:43:25]:
Yeah, so that's what I use and it's great. I love it.
Steve Gibson [01:43:28]:
Y so this wonderful call to Action Paper next offers some key takeaways for CISOs. Here's what the paper's authors recommend CISOs to consider. You use LLM based vulnerability discovery and remediation capabilities. They said unlike defensive AI technologies, LLM based vulnerability discovery capabilities are already mature and could be used to your advantage. Start immediately by asking an agent for a security review of any code and build towards a vuln ops capability. Update your risk metrics with the shifting landscape, many of your metrics and risk assessments may be outdated and could affect business reporting. Consider how to update these and communicate the challenge with stakeholders. Accelerate your team by the use of coding agents and you got you were just talking about this on MacBre on Mac Break weekly how some group at
Leo Laporte [01:44:38]:
Apple, the Siri group, is being sent to learn how to vibe code. Almost 200 of them because I guess they weren't. They didn't, they didn't take it seriously. Take it seriously.
Steve Gibson [01:44:51]:
They didn't realize what the benefits were. So these guys are saying to CISOs, accelerate your team by the use of coding agents. While defensive AI technologies are lagging behind offensive ones, agents can already accelerate human action across the board from incident response to grc. Encourage and require your team to use these agents to accelerate their capabilities. Triage and test patches. Red Team your environment, automate audit data collection and accelerate security operations overall. Prepare to respond to more incidents. Run tabletop exercises for multiple simultaneous high vulnerability incidents occurring within the same week and have playbooks in place for high level critical incidents.
Steve Gibson [01:45:47]:
I mean these guys are literally predicting a storm is coming. Examine how to automate remediation capabilities to the degree possible. Verify and enable mitigating controls such as segmentation, egress filtering, zero trust architectures, phishing, resistant, multi factor authentication and secrets rotation to limit impact. When exploitation occurs, the supply chain will be affected. Increase focus on the basics. The basics remain valid and can be prioritized for risks that cannot otherwise be mitigated. Segmentation, patching known vulnerabilities, identify and identity and access, management and defense in depth and breadth all increase the difficulty for attackers to lower latent risk. Expanding these efforts while there is time is prudent.
Steve Gibson [01:46:45]:
In other words, do it now before it's too late. They said we cannot outwork we cannot outwork machine speed threats. Reprioritize, automate and prepare for burnout. The cadence and volume of vulnerability disclosures will exceed anything we have experienced before. I mean they're, they're literally saying understand everybody, bad guys, China and Russia and North Korea. They're going to get this capability and they are going to come at us hard, they wrote. The cadence and volume of vulnerability disclosures will exceed anything we have experienced before. Consider how you manage current priorities and request additional headcount and budget for reserve capacity to avoid exhausting available resources or potentially burning out existing staff.
Steve Gibson [01:47:47]:
This in parallel with adoption of coding agents, reprioritization, putting more automation in place and helping your team through career uncertainties and upskilling challenges. Yikes. Evolve to a Mythos Ready security program. Mythos, they wrote, is likely one of many changes coming to cybersecurity risk, if not already underway. Seriously consider incorporating Mythos and its implications into your strategy. Build collective defense Now. Attackers are already operate already operate as syndicates, crowdsourcing, sharing tools and moving as a collective. Engage now with sector coordinating groups, ISACs, CERTs and standards bodies to share threat intelligence, coordinate response and produce sector specific guidance.
Steve Gibson [01:48:50]:
For this moment, Defenders must do the same and leverage our coordinating groups, especially when considering organizations that fall below the Cyber Poverty line as introduced by Wendy Nather. So just to pause, A little over three years ago, back in 2023, Cisco's CISO Wendy Nather articulated a concept she termed the Cyber Poverty Line. It was the point below which an organization cannot afford to invest in the minimum required security to remain safe on the Internet. So like you, you don't do need to invest in security. The bottom of page 17 of the show notes duplicates a breathtaking chart from the very cool and somewhat unnerving website0dayclock.com you know Z R O D A Y c l o c-k.com the chart shows how the vulnerability versus exploit race has radically changed over just the past eight years. Eight years. At the bottom of page 17 a beautiful chart. Eight years ago in 2018, the average TTE time to exploit was 2.3 years.
Steve Gibson [01:50:18]:
In other words, just eight years ago on average there was a 2.3 year gap between the public disclosure of a security vulnerability in a CVE and its confirmed use in an attack exploit. 2.3 years.
Leo Laporte [01:50:38]:
Wow. We had a lot of time back in the day.
Steve Gibson [01:50:41]:
We did not anymore. Look at this chart Leo at the bottom of page 17.
Leo Laporte [01:50:46]:
How many days now do we have in a zero day?
Steve Gibson [01:50:49]:
Well watch how this Happens the next year. In 2019, that exploitation gap had dropped from 2.3 to 1.9 years. In 2020, a year later it was down to 1.3 years to exploit. 2021 averaged 10.8 months from CVE publication to exploitation. A year later, 2022 dropped that 10.8 months down to 9.7. The next month 4.9. I mean, sorry, the next year, 2023 was down to 4.9 months. 2024, just two years ago, we were down to 56 days.
Steve Gibson [01:51:36]:
Last year, 23.2 days. And shockingly, so far this year we are seeing exploits appear an average of 10 hours after their CVE vulnerabilities have been published.
Leo Laporte [01:51:54]:
That's AI, right? I mean that's got to be AI.
Steve Gibson [01:51:56]:
That is, that is. And we've been talking about this on the podcast mostly theoretically because it was obvious it was going to happen. Bad guys are sitting waiting for new vulnerabilities to be published and they instantly jump on them and they, they 10 hours. And so, so I mean there is just no time. As the, as the writers of this paper said, humans cannot outperform machine driven attacks. It can't, it won't. It doesn't happen. So from.
Steve Gibson [01:52:34]:
Think about that. Eight years, Leo, gone from 2.3 years to, to 10 hours. So everybody should check out the zero day clock dot com. It's got this chart and a bunch of others where, where these sorts of stats are, are being maintained and it is breathtaking. Okay, so next I'm going to share just the brief introduction that these cybersecurity industry expert authors wrote for the paper. But Leo, let's first take our final brick thinking.
Leo Laporte [01:53:07]:
Thank you for remembering, Steve. All right, on we go. Oh, Steve, I think you're muted again.
Steve Gibson [01:53:15]:
Did it again. I didn't want you to hear me typing, so.
Leo Laporte [01:53:19]:
No problem.
Steve Gibson [01:53:19]:
Okay, thank you. Okay, so the brief introduction that these cybersecurity industry expert authors wrote for the paper, they explain and, and I'll. Well, I'm going to point our listeners and our list are to recommend that they point their bosses. Anybody who doesn't understand this. The. The paper was written for the C suite guys to, to understand and that's why it's got the who's who behind it. So they wrote many of our assumptions about the capabilities of AI and in vulnerability research, exploitation and autonomous attacks may be outdated. Throughout 2025 and into 2026, we've seen continuous examples of increasing capabilities both in research and in actual in the wild attacks, AI driven vulnerability discovery and exploitation has been accelerating for over a year.
Steve Gibson [01:54:25]:
Anthropic's Claude Mythos Preview represents a step change in that trajectory. Autonomously finding thousands of critical vulnerabilities across every major operating system and browser, generating working exploits without human guidance, and empowering autonomous attack orchestration, all at a speed and scale that outpaces any prior capability. The asymmetry this creates is structural. AI lowers the cost and skill floor for discovering and exploiting vulnerabilities faster than organizations can patch them. This is what I was talking about last week when I said, you know, now script kiddies can be expert attackers and exploiters because you just ask AI. For some attacks, the window between discovery and weaponization has collapsed to hours. Attackers gained disproportionate benefit, and current patch cycles, response processes and risk metrics were not built for this environment. While many of these capabilities predate this model, Mythos class capabilities do represent a step change and will proliferate.
Steve Gibson [01:55:48]:
Meaning Anthropic is only first, they're not the last. The organizations that respond well will be those that build the muscle now, the processes, the tooling, and a culture willing to adopt AI as a core part of how security gets done. The adaptability will help determine who meets the next wave on their own terms. This moment requires reprioritizing resources, reviewing risk levels and controls, and leveraging AI where feasible. At the time of this writing, most AI defensive controls and approaches are not yet mature. That said, AI attacker technology may be used for defense purposes, and coding agents will help. Okay, and to finally place all this into context, I want to share Appendix A of their paper, which they titled Historical President Precedent, meaning where we came from. Because this, this will sort of help everybody to put this in context, they said.
Steve Gibson [01:56:55]:
This all began with the DARPA Cyber Grand Challenge, a landmark competition organized by DARPA in 2016. So a decade ago that demonstrated the potential of fully automated cybersecurity systems. Teams developed autonomous platforms capable of identifying, exploiting and patching software vulnerabilities in real time without human intervention. The challenge highlighted a shift toward machine speed cyber defense, showing how automation and artificial intelligence could significantly enhance vulnerability management and incident response, while also raising important questions about trust, control and the future role of human operators in cybersecurity, meaning humans are going to be obsolete by mid-2025. Expo, an autonomous offensive security company, topped the HackerOne leaderboard. The DARPA AI Cyber Challenge found 54 vulnerabilities in four hours of compute. Google's Big Sleep discovered real zero days in open source anthropic was used to automate full attack chains from reconnaissance through exfiltration and open source tools such as Raptor proved autonomous vulnerability research is available to anyone able to use an agent in September 25, Heather Atkinson, the CISO for Google, and Gaddy Evron, the CEO of Gnostic, published a warning. Okay, September 2025 they published a warning that attackers were racing toward a singularity moment with autonomous vulnerability discovery and exploitation roughly six months away.
Steve Gibson [01:58:56]:
Wow. Well that's impressive. Their timing was exactly correct. That was six months ago. In February 2026, Anthropic used Claude Opus 4.6 using Claude Opus 4.6 reported more than 500 high severity vulnerabilities in open source software. Aisle remember AI sle Aisle found 12 open SSL zero days including a CVSS 9.8 vulnerability dating back to 1998. Linux kernel maintainers saw vulnerability reports climb from 2 to 10 per week, largely hallucinated at first, but that changed rapidly. The volume has held steady, but the reports are now all verified as real bugs.
Steve Gibson [01:59:55]:
The Curl project, which originally discontinued its bug bounty program because it was drowning in hallucinated vulnerability reports AI Slop last week echoed the observation from the Linux team reporting an increasing number of AI supported high quality security incidents. Sysdig documented an AI based attack that reached admin level access in 8 minutes. This week Gambit released a report on the AI led compromise of Mexican government infrastructure originally reported in February and actually I I saw that and skipped over reporting that due to show length but briefly, an attacker used a combination of both chat, GPT and CLAUDE to attack rapidly penetrate inventory and exfiltrate a much larger amount of data from the Mexican government than would have ever been possible without the aid of AI automation. He used an AI automated based attack. So they end their historical timeline by telling us about the zero day clock. Writing in March, Sergev Epp and others introduced the zero day clock, visually demonstrating the disappearing time to exploit development, demonstrating the drastic fall in time to exploitation to less than a day in 2026. Yeah, 10 hours. It's worth noting that the historical collapse in time to exploit has not yet produced a proportional increase in the impact of exploitation.
Steve Gibson [02:01:42]:
Many of the most consequential incidents of recent years involved credential abuse, social engineering or supply chain compromise rather than zero days. The zero day clock trend is a leading indicator of where attacker capability is heading, not a direct measure of current damage. So it's predicting what's going to happen shortly. The AI driven okay, so then the AI driven security research company Aisle AI SLE Remember that we talked about them at the time. They found the problems in open ssl. They responded a little disgruntled themselves, understandably to all of the Mythos buzz. And so it was in February that we reported on them finding those 15 vulnerabilities in Open SSL, 12 of which entirely composed a major update to Open SSL. And as we know, this paper briefly mentioned them in passing.
Steve Gibson [02:02:52]:
They're grumbling somewhat, saying that they were able to reproduce anthropic results themselves without the mythical Mythos. They wrote, and I have a link to them to their report. In the show notes they said, we took this is aisle, we took the specific vulnerabilities anthropic showcases in their announcement, isolated the relevant code and ran them through small cheap open weight models. Those models recovered much of the same analysis. Eight out of eight models detected Mythos flagship FreeBSD exploit, including one with only 3.6 billion active parameters costing 0.$11 per million tokens. A 5.1 billion active token open model recovered the core chain of the 27 year old OpenBSD bug. And on a basic security reasoning task, small open models outperformed most frontier models from every major lab. The capability rankings reshuffled completely across tasks.
Steve Gibson [02:04:14]:
There is no stable best model across cyber security tasks. The capability frontier is jagged. In other words, they're just saying, hold on here, you know, we've got our own small cheap models that we are able to deploy that do the same thing as Mythos. And I don't doubt what aisle that aisle did what they claimed, although admittedly there's much they didn't say. For example, even with isolated code, confirming an already known problem feels different from making brand new discoveries. Although I know in theory it should. There should be no different. We also don't know how autonomous their system was.
Steve Gibson [02:05:02]:
That was one of the main points that Anthropic has been making about Mythos is that you just ask it pretty much pretty please to attack somebody and it's able to. And it's only natural for aisle a commercial enterprise whose specific and narrow focus is to offer commercial vulnerability discovering services to enterprise. To be somewhat miffed over all the breathless industry and media coverage Mythos has generated, they should be celebrating their own systems if they're able to meaningfully compete with Mythos outcome for far less money. As I said, once the dust, the dust has settled, it's gonna all come down to who can do the most with the fewest resources. So if, if I'll got some bunch of tricks up their sleeve that allows them to offer these services much less expensively, far more economically than I say that's great. Bravo. However, everyone who's been paying attention knows that what the cyber security industry most needs right now, this instant, without delay, is a swift kick in the pants. This Security now podcast informed its listeners of IELTS AI Driven Vulnerability Discovery news back in February.
Steve Gibson [02:06:32]:
It's one of the reasons that Anthropic's claims for Mythos made so much sense to us, right? Because like, we saw this coming, you know, this made sense. But IO did not break through in February. Mythos did. Even if Mythos were hype, which none of these experts who should know believe it to be, it should be abundantly clear, even looking at Aisle's results with open SSL from February, that the next stage of AI Driven Rapid Vulnerability discovery and exploitation is here now. And that, as all of these expert also agreed, we're not ready for it. So I'm all for the hype this industry is able to muster if it will help to instill some much needed fear and action from an industry which appears to have become far too comfortable with the status quo. You know, as I said at the top and a couple times, let's turn this. Let's have another Y2K event.
Steve Gibson [02:07:42]:
This, that never happens. Not because it isn't real, but because it is. And everyone who needed to. Who needed to, who needed to understood and then took action to prevent the apocalypse from ever happening when. When everything rolled over to the year 2000. Anyway, as I said, I've created two GRC shortcut links to this very significant paper to make it even easier for our listeners to get to it. You can either go to GRC SC Mythos M Y T H O S, which everyone should be able to remember, and that'll just bounce you over to the PDF or this, this week's episode number GRC SC 1075. That'll do the same thing.
Leo Laporte [02:08:31]:
Nice.
Steve Gibson [02:08:31]:
And I think it is very clear that the. I mean, I get it that when we're talking about increasing headcount and reshuffling priorities and all this, I mean, these are expensive things to ask for a problem that hasn't yet manifested. The problem is by the time it does, it could be too late.
Leo Laporte [02:08:53]:
It's like a lot more expensive.
Steve Gibson [02:08:55]:
Yes, it's like waiting to see what, you know, like if the elevators stop running on January 1st of the year 2000. Like, I'd rather not get stuck in an elevator, thank you very much.
Leo Laporte [02:09:07]:
Okay, now here's the question, models are going to continue to get better. I think there's no doubt about that. There was some question a year ago maybe that maybe we'd hit a plateau and models weren't getting better fast. I think we all see that, that.
Steve Gibson [02:09:22]:
And we're learning how to use this new thing.
Leo Laporte [02:09:24]:
Yeah.
Steve Gibson [02:09:25]:
Like the notion of parallel agents.
Leo Laporte [02:09:27]:
Yeah, we're getting better at it.
Steve Gibson [02:09:29]:
And a collection, a collection of different capabilities that are brought in.
Leo Laporte [02:09:33]:
Right.
Steve Gibson [02:09:34]:
So, yeah, so we're learning basically how to ask.
Leo Laporte [02:09:37]:
So presumably the 271bugs we found in Firefox this time, next time we might find more. We might find more again. As models get better, we might find more again. Is there a point where software just becomes perfect and there are no more bugs or. I think there is.
Steve Gibson [02:09:56]:
Yeah. I think there is. It. Software is Math. Math is 100 predictable.
Leo Laporte [02:10:04]:
Right.
Steve Gibson [02:10:05]:
You know, there's, there's, there's no random number generator that like, like there is in AI. There's no, there's no random number generator in our software. You know, it is deterministic. And, and I hold that if that's something that doesn't get lost in the details, basically humans have created software that is too complex for them to hold in their head.
Leo Laporte [02:10:30]:
Right.
Steve Gibson [02:10:31]:
That that's what's happened is we don't understand our own creation. But AI can be scaled to be able to understand, you know, and I use understanding air quotes. I know it's not conscious, it's not actually understanding. But, but, but to weave through all the combinatorial ins and outs and, and God. Who was it? There was another person who. I just saw it. I think it might have been in an email feedback. Somebody else.
Steve Gibson [02:11:01]:
Oh, it was one of our listeners. I, I'll share it next week. It was one of our listeners who has been maintaining a package that is exposed to the Internet and it involves SQL. And he was curious. So he aimed Claude code at the software that he wrote and it found a vulnerability that astonished him. And he said it wasn't super critical because it only. Blah, blah, blah, blah, blah. I know there were lots of ways that you had to have it, but he was amazed by what it found in his own code.
Steve Gibson [02:11:38]:
And so he stood there thinking, my God, did it. Is this true? And then he actually. Oh, he didn't want to upset it by asking it for an exploit, so he wrote the exploit himself.
Leo Laporte [02:11:51]:
Actually, Glenn Fleischman on Sunday was reporting something very similar. He's had web facing or Internet facing tool running for, I think he said like 20 years a long time. It's just a little thing that he runs some sort of a book search or something. And he said he, you know, fired Claude code at it. It found bugs that had been running for 20 years. No one's seen, he hadn't seen that he was able to fix. I mean, I think you nailed it, which is that it's gotten impossible for us as human beings to make perfect software. But this is a machine.
Leo Laporte [02:12:28]:
It is tireless. It doesn't make the same kinds of mistakes.
Steve Gibson [02:12:32]:
And use chess. Fall back to chess again. You know, super chess grandmasters are able to look at a board and, and see things in it I can't even begin to describe.
Leo Laporte [02:12:45]:
Right.
Steve Gibson [02:12:46]:
They, they were able to hold their own for a long time. No more.
Leo Laporte [02:12:50]:
No, that's gone. It's no longer even close.
Steve Gibson [02:12:52]:
And that, that suggests that now we have, we have computers that are able to look at the same thing again. There's no, no one's rolling dice in chess. It is deter.
Leo Laporte [02:13:04]:
A.
Steve Gibson [02:13:04]:
Determine a deterministic board game. And, and they can take us down now.
Leo Laporte [02:13:09]:
Meanwhile, I've been working on my firmware. Let me just. Help me Obi Wan. Help me Obi Wan. Just gonna see if it's listening. Help me Obi Wan. Still working on it. It's a very.
Leo Laporte [02:13:19]:
It's a thorny problem we're, we're working on here.
Steve Gibson [02:13:22]:
But we are, you know, we're. Okay. You're a little younger than I am. You're in your late 60s. I'm now 71.
Leo Laporte [02:13:31]:
No, I'm almost 70. I'll be 70 in November. I'm not so far behind.
Steve Gibson [02:13:34]:
Okay, so we're still going to be here in another 10 years. I hope so.
Leo Laporte [02:13:39]:
God willing.
Steve Gibson [02:13:39]:
The world is going to be different.
Leo Laporte [02:13:41]:
I know, and I love that. I thought I was going to miss the apocalypse.
Steve Gibson [02:13:45]:
It's going to happen so fast that what's so cool is there's so much money behind software development that there will be a huge push to make this happen.
Leo Laporte [02:13:55]:
Oh, yeah. And the other thing that's encouraging is this. These tools are getting more efficient, which means they're taking less hardware to do more, which means not only will they improve, but they will be more accessible. They will be less expensive.
Steve Gibson [02:14:10]:
I'm convinced cloud crap is going to go away. We're going to have local running models because we'll have little software AI boxes in our homes that we talk to and they're able to do what we want.
Leo Laporte [02:14:23]:
Yep, yep. That's what I'm working on right now. That's exactly it. I'm trying to make because I'm so dissatisfied with Alexa and Siri and all these other assistants. I'm trying to make an assistant that works the same way, but is local and knows me and has memory and all of that stuff. And I'm getting closer than I ever thought I would. And I think, you know, by the time.
Steve Gibson [02:14:45]:
And here's the key, Leo. You are having fun.
Leo Laporte [02:14:48]:
Oh, and it's so. It's the best game ever. You are having fun.
Steve Gibson [02:14:51]:
Yep.
Leo Laporte [02:14:52]:
It's similar. I mean, I still love coding, but coding is more like hand building furniture.
Steve Gibson [02:14:57]:
Leo. It is modern coding. This is what coding is going to become. People are going to be removed from the code generating loop and we, and we will be directing AI to write our code.
Leo Laporte [02:15:09]:
Yes.
Steve Gibson [02:15:09]:
And this is me who's still coding in, in assembly language. I'm saying it's over, folks. People are going to be taken out.
Leo Laporte [02:15:17]:
Wow. And you know what? Maybe, maybe that's the right thing because
Steve Gibson [02:15:21]:
we had our time.
Leo Laporte [02:15:23]:
The computers are going to do a better job of this. This is their native tongue. You know, Steve Gibson does such a good job. I'm so glad we have you to rely on. And let's, let's hope we get to keep doing this for many, many more years to come. You'll find him@grc.com the Gibson Research Corporation. That's where you'll find Spinrite, the world's best mass storage maintenance, performance enhancing and recovery tool. If you've got mass storage, you got to have Spinrite.
Leo Laporte [02:15:52]:
Get the current version 6.1. Is there free upgrades for anybody who's ever bought it in the past? If you haven't bought it, buy it now. Get on the train. He also has something brand new that he wrote that's fantastic. The DNS Benchmark Pro that lets you figure out what the best DNS provider would be for your particular situation.
Steve Gibson [02:16:13]:
It matters where you live.
Leo Laporte [02:16:14]:
It's less than 10 bucks. Matters where you live. All of that@grc.com While you're there, sign up for his newsletters. He has two of them. One is a product announcement newsletter that you'll never get anything from because he works very carefully.
Steve Gibson [02:16:29]:
Methodically.
Leo Laporte [02:16:30]:
Methodically. The other though, you will get a weekly email. The show notes, sometimes from the wrong year. Most of the time from the right year. No, it's always the correct show notes. It's just the year that it says it's from is different. And those come out usually on a Sunday before the show on Tuesday or thereabouts so sign up there@grc.com email you're actually what you're really doing. That form there is just a whitelist your email so you can send him pictures of the week and comments and suggestions and stuff.
Leo Laporte [02:17:01]:
You do have to do that because he doesn't want any spam. It's a very effective system he's come up with. Let's see what else. Oh, we have copies of the show at our website, Twitter TV SN. There's also a YouTube channel dedicated to the video. You can also subscribe and you're favorite podcast client. However you do it, I don't think you want to miss a single episode of this show. And if you're one of those folks who wants the most recent version of the show, you can actually watch us do it live Tuesdays right after Mac break weekly.
Leo Laporte [02:17:30]:
That's 1:30 Pacific, 4:30 Eastern 20:30 UTC. Club members get to watch in the club Twit Discord. How nice. The rest of you can watch on YouTube, Twitch, X.com, facebook, LinkedIn or Kik. You take your pick. So you can watch live if you want. If you're not a club member, do join the club. Very important to us to keep doing what we're doing.
Leo Laporte [02:17:55]:
Advertising does not cover all of our expenses. Barely covers 70%. The club makes up the difference and without you we really wouldn't be able to do what we're doing. So please think about it. If you can afford it, 10 bucks a month you get ad free versions of all the shows. You get access to Discord, which is a great place, smart people, really fun to hang out. You get special programming just for club members. We really need you now more than ever.
Leo Laporte [02:18:20]:
Twit TV Club Twit Steve. Have a wonderful week and we'll do next time.
Steve Gibson [02:18:28]:
I'll be here next Tuesday. Bye
Leo Laporte [02:18:33]:
security.
Steve Gibson [02:18:34]:
Now.